You’ve heard the horror stories about data breaches, stolen payment data, and vulnerable ecommerce platforms.
For businesses planning to launch a white-label Chewy app, security is one of the biggest concerns. Pet ecommerce platforms handle customer profiles, payment data, shipping addresses, and subscription orders, which makes them attractive targets for cybercriminals.
In 2026, ecommerce security risks are higher than ever. Global reports show that over 43% of cyberattacks now target ecommerce platforms, especially apps handling recurring payments and user accounts.
So the real question is simple:
Is a white-label Chewy app actually safe?
The honest answer depends on how the platform is built, the security standards followed, and the provider you choose.
In this guide, we’ll break down:
- The real security risks of white-label Chewy apps
- Compliance and security standards required in 2026
- How to identify unsafe providers
- Best practices to protect your users and business
We’ll also show how security-first development from Miracuves helps businesses launch safe, compliant ecommerce apps.
Understanding White-Label Chewy App Security Landscape
What White-Label Security Actually Means
A white-label Chewy app is a ready-made ecommerce platform that businesses can customize with their own branding, products, and features. Instead of building an app from scratch, companies launch faster using a pre-built infrastructure.
From a security perspective, this means the foundation of the app — backend systems, APIs, payment integrations, and databases — is developed by the provider.
Security responsibility is usually shared between:
- The platform provider (core infrastructure and code security)
- The business owner (data handling, policies, and operations)
If the platform is poorly built, every business using it inherits the same vulnerabilities.
That is why choosing a security-focused provider becomes critical.
Common Security Myths vs Reality
Many businesses misunderstand how white-label security works. Some fears are justified, while others are misconceptions.
| Myth | Reality |
|---|---|
| White-label apps are always insecure | Security depends on development standards and infrastructure |
| Custom-built apps are automatically safer | Poorly built custom apps can be more vulnerable |
| Security is only about encryption | Security includes infrastructure, APIs, compliance, and monitoring |
| Small ecommerce apps are not targets | Automated attacks target platforms of all sizes |
In reality, most ecommerce breaches happen because of weak implementation rather than the business model itself.
Why People Worry About White-Label Apps
Businesses considering a white-label Chewy app often worry about several issues.
Shared infrastructure risks
If the platform runs multiple apps on the same servers, one vulnerability could affect many businesses.
Unknown code quality
Companies cannot always see the underlying source code, which makes it difficult to evaluate security practices.
Third-party integrations
Pet ecommerce apps often integrate with:
- Payment gateways
- Shipping providers
- Subscription billing systems
- Inventory management tools
Each integration increases the attack surface.
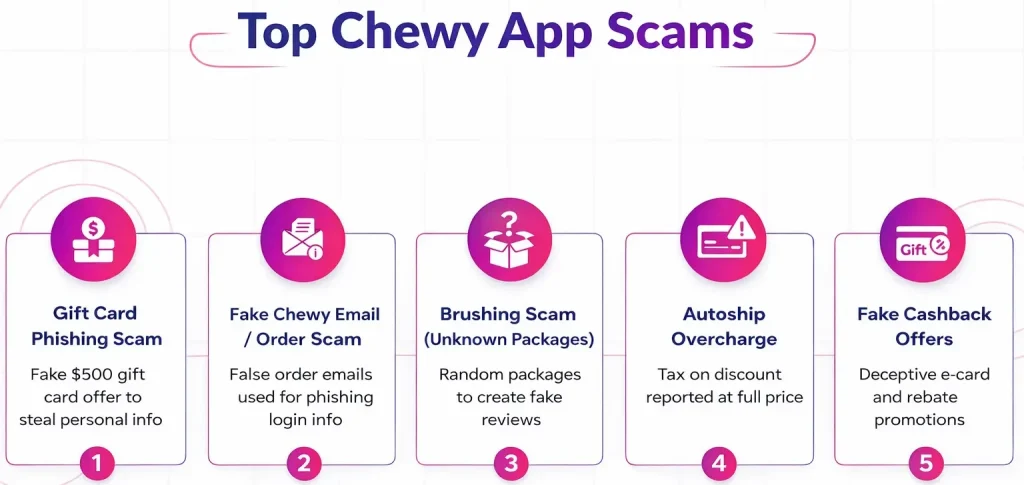
Current Threat Landscape for Pet Ecommerce Apps
Pet ecommerce platforms like Chewy-style apps handle sensitive user and payment data, making them common targets.
Subscription-based ecommerce apps are particularly attractive to attackers because they store long-term payment credentials.
Security Standards Expected in 2026
In 2026, ecommerce platforms are expected to follow strict security practices.
Key expectations include:
- End-to-end encryption for sensitive data
- Secure API architecture
- Tokenized payment processing
- Real-time fraud detection
- Multi-factor authentication for users and admins
Modern platforms also implement Zero Trust architecture, where every system interaction is verified.
Real-World App Security Statistics
Recent cybersecurity research highlights how serious the problem has become.
- 43% of cyberattacks target small and medium businesses
- Ecommerce platforms face 32% more bot attacks than other industries
- Credential stuffing attacks increased by 38% in 2026
- Average cost of a data breach reached $4.7 million globally
These statistics show that security is no longer optional for ecommerce apps.
Businesses launching a white-label Chewy app must treat security as a core product feature, not an afterthought.
Key Security Risks & How to Identify Them
White-label Chewy apps manage sensitive data such as customer accounts, pet product orders, shipping details, and payment information. Because of this, several security risks must be carefully evaluated before launching the platform.
Understanding these risks helps businesses detect vulnerabilities early and implement stronger protections.
Data Protection and Privacy Risks
User Personal Information
Pet ecommerce platforms collect large amounts of personal data including names, phone numbers, addresses, and purchase history.
If this data is stored without proper encryption or access controls, attackers can steal it through database breaches.
Common causes include:
- Weak database security
- Poor authentication systems
- Misconfigured cloud storage
Data protection laws in 2026 require companies to apply strict controls when handling user data.
Payment Data Security
A Chewy-style app processes online payments for pet food, supplies, and subscription deliveries. Payment data is one of the most valuable targets for cybercriminals.
Risks appear when apps use:
- Non-PCI compliant payment systems
- Direct card storage instead of tokenization
- Insecure checkout APIs
Secure apps use payment tokenization so that card details are never stored on the platform.
Location Tracking Concerns
Many ecommerce apps collect location data for delivery tracking and logistics.
If location APIs are not protected properly, attackers could access:
- Real-time delivery routes
- Customer addresses
- Order history linked to locations
This creates privacy risks and potential legal violations under modern data protection laws.
GDPR and CCPA Compliance
Businesses operating internationally must comply with global privacy regulations.
Key requirements include:
- User consent for data collection
- Clear privacy policies
- Secure storage of personal data
- Ability for users to delete their data
Failure to follow these regulations can result in major penalties.
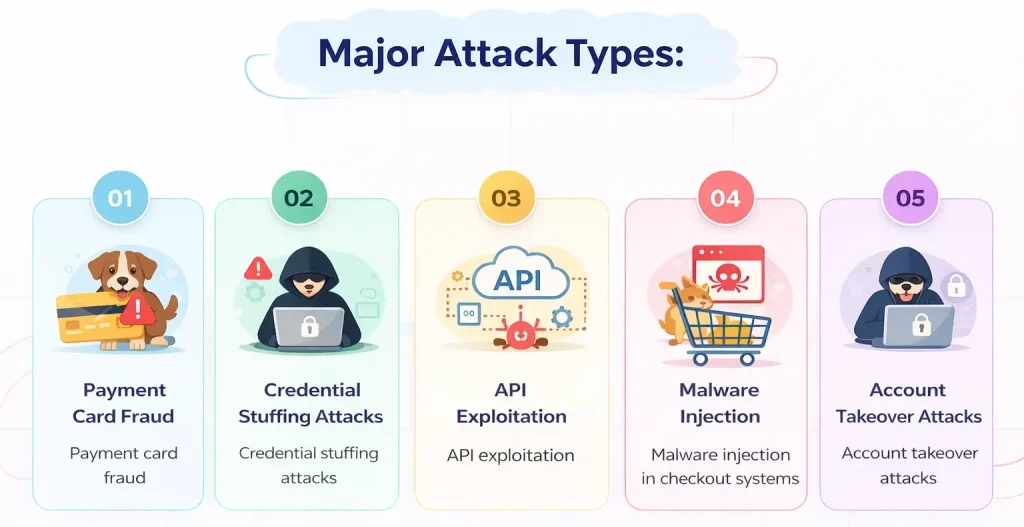
Technical Vulnerabilities
Code Quality Issues
Poorly written code creates hidden vulnerabilities. Many attacks exploit basic mistakes such as:
- SQL injection
- Cross-site scripting
- Improper authentication logic
A secure white-label app must follow secure coding practices and undergo regular code reviews.
Server Security Gaps
Backend infrastructure is one of the most common attack points.
Risks appear when servers have:
- Weak firewall rules
- Open ports
- Unpatched operating systems
- Poor cloud configuration
Modern platforms use hardened infrastructure with strict access control.
API Vulnerabilities
APIs connect mobile apps, websites, payment gateways, and logistics systems.
If APIs lack proper authentication or rate limiting, attackers may exploit them to:
- Extract customer data
- Manipulate orders
- Launch automated attacks
Secure API design includes authentication tokens, encryption, and request validation.
Third-Party Integrations
Pet ecommerce apps often integrate with external systems such as:
- Payment gateways
- Shipping providers
- CRM platforms
- analytics tools
Each integration introduces additional security risk if the third-party provider has vulnerabilities.
Business Risks
Legal Liability
If a breach exposes customer data, the business operating the app may be legally responsible.
Regulators can impose fines, especially when companies fail to implement required security measures.
Reputation Damage
Trust is essential for ecommerce platforms. A public data breach can severely damage brand reputation.
Customers often abandon platforms that fail to protect their personal information.
Financial Losses
Security incidents create several financial impacts:
- breach investigation costs
- legal expenses
- regulatory penalties
- customer compensation
Many companies also lose revenue due to downtime during an attack.
Regulatory Penalties
Authorities worldwide have increased enforcement of privacy laws.
Penalties may reach millions of dollars depending on the severity of the violation.
White-Label Chewy App Risk Assessment Checklist
Businesses should evaluate the following areas before choosing a white-label provider.
| Security Area | What to Check |
|---|---|
| Data Protection | Encryption for stored and transmitted data |
| Payment Security | PCI DSS compliant payment processing |
| Infrastructure | Secure cloud hosting and server hardening |
| API Security | Authentication tokens and rate limiting |
| Compliance | GDPR and regional privacy law compliance |
| Monitoring | Real-time threat detection systems |
| Backup Systems | Automated backup and disaster recovery |
Performing a thorough risk assessment helps businesses avoid unsafe platforms and choose providers with strong security foundations.
Read more : – Business Model of Chewy : Complete Strategy Breakdown 2025
Security Standards Your White-Label Chewy App Must Meet
Launching a white-label Chewy app without proper security standards can expose both the business and its users to serious risks. Modern ecommerce platforms must follow internationally recognized security frameworks.
In 2026, investors, regulators, and customers expect strict compliance with global security certifications and technical protections.
Essential Security Certifications
ISO 27001 Compliance
ISO 27001 is one of the most widely recognized information security standards. It focuses on building a strong Information Security Management System.
Platforms following ISO 27001 implement:
- structured risk management processes
- strict access control policies
- continuous monitoring of security threats
- documented security procedures
For ecommerce platforms handling customer data, ISO 27001 certification demonstrates strong operational security.
SOC 2 Type II Certification
SOC 2 Type II verifies that a platform follows strict controls for protecting customer information.
The certification evaluates five key areas:
- security
- availability
- processing integrity
- confidentiality
- privacy
For a white-label Chewy app provider, SOC 2 Type II proves that the platform maintains secure infrastructure over time.
GDPR Compliance
Any app serving customers in the European Union must follow GDPR requirements.
GDPR requires businesses to:
- collect user data with explicit consent
- store data securely
- allow users to request deletion of their information
- report breaches quickly to regulators
Failure to comply can result in large financial penalties.
HIPAA Compliance (If Applicable)
Some pet ecommerce platforms integrate veterinary consultations or health-related services.
If the app stores or processes pet medical data connected to veterinary providers, additional healthcare data protection standards may apply.
In such cases, HIPAA-level security practices may be required.
PCI DSS for Payment Processing
Payment Card Industry Data Security Standard is mandatory for any platform processing credit card transactions.
PCI DSS requires:
- encrypted card transactions
- secure network architecture
- restricted access to payment data
- regular security testing
Most modern platforms use payment tokenization so card data is never stored directly in the app.
Technical Security Requirements
Beyond certifications, strong technical protections are necessary to secure a white-label Chewy app.
End-to-End Encryption
Sensitive information must be encrypted both during transmission and when stored.
This protects data such as:
- customer login credentials
- payment details
- shipping addresses
- order history
Encryption prevents attackers from reading stolen data.
Secure Authentication Systems
Secure login systems reduce the risk of account takeover attacks.
Modern apps should implement:
- multi-factor authentication
- OAuth authentication systems
- secure password hashing
- login anomaly detection
These protections help prevent unauthorized access.
Regular Security Audits
Security audits help identify vulnerabilities before attackers do.
Professional security teams review:
- code quality
- infrastructure configuration
- API security
- database protection
Regular audits are an essential part of maintaining a secure platform.
Penetration Testing
Penetration testing simulates real cyberattacks to evaluate system defenses.
Security specialists attempt to exploit weaknesses in:
- application code
- network infrastructure
- authentication systems
- third-party integrations
These tests help identify critical vulnerabilities.
SSL Certificates
SSL encryption ensures that all communication between the user and the app remains secure.
Without SSL protection, attackers could intercept sensitive data during transmission.
Secure ecommerce platforms enforce HTTPS across all services.
Secure API Design
APIs connect the app with payment systems, shipping services, and databases.
Secure APIs must include:
- authentication tokens
- request validation
- rate limiting
- encrypted communication
Poorly designed APIs are one of the most common causes of data leaks.
Security Standards Comparison Table
| Security Standard | Purpose | Why It Matters for a Chewy App |
|---|---|---|
| ISO 27001 | Information security management | Protects business data and operational security |
| SOC 2 Type II | Infrastructure security validation | Ensures platform reliability and data protection |
| GDPR | Data privacy regulation | Protects user data and ensures legal compliance |
| PCI DSS | Payment card protection | Secures customer payment information |
| SSL Encryption | Secure data transmission | Prevents interception of sensitive data |
| Penetration Testing | Vulnerability detection | Identifies weaknesses before attackers |
Meeting these standards ensures that a white-label Chewy app is built on a secure and compliant foundation.
Businesses that ignore these requirements significantly increase their risk exposure.
Red Flags: How to Spot Unsafe White-Label Providers
Choosing the wrong white-label Chewy app provider can expose a business to security vulnerabilities, compliance violations, and financial losses. Many security problems start with providers that cut corners during development or infrastructure setup.
Understanding warning signs early can help businesses avoid unsafe platforms.
Major Warning Signs to Watch
No Security Documentation
A reliable provider should clearly explain its security practices.
If a company cannot provide documentation about:
- encryption methods
- infrastructure security
- data protection practices
- compliance certifications
then the platform may not follow professional security standards.
Transparent documentation is a basic requirement for any secure ecommerce system.
Unrealistically Cheap Pricing
Building a secure ecommerce app requires investment in infrastructure, security audits, and compliance.
Providers offering extremely low prices may be skipping critical components such as:
- security testing
- server hardening
- compliance implementation
Cheap platforms often lead to higher long-term risks.
No Compliance Certifications
A secure provider should follow recognized security frameworks.
If the provider cannot demonstrate compliance with standards such as:
- ISO 27001
- SOC 2
- GDPR data protection
- PCI DSS payment security
then the platform may not meet modern regulatory expectations.
Outdated Technology Stack
Older frameworks and unsupported software often contain known vulnerabilities.
Warning signs include:
- outdated backend frameworks
- unsupported operating systems
- deprecated payment integrations
- lack of modern authentication systems
Modern security requires continuously updated technology.
Poor Code Quality
Low-quality code creates security holes that attackers can exploit.
Indicators of weak development practices include:
- frequent app crashes
- slow performance
- inconsistent features
- poorly structured APIs
Professional development teams follow secure coding standards and maintain structured codebases.
No Security Updates Policy
Cyber threats evolve constantly. Secure platforms release regular security updates.
If a provider does not have a clear update policy, the app may become vulnerable over time.
Regular updates should include:
- vulnerability patches
- dependency upgrades
- infrastructure improvements
Lack of Data Backup Systems
Data loss can occur due to cyberattacks, server failures, or accidental deletion.
Secure providers implement automated backup systems that allow rapid recovery.
A reliable backup strategy should include:
- automated daily backups
- encrypted storage
- disaster recovery planning
No Insurance Coverage
Many enterprise-grade technology providers carry cyber liability insurance.
Insurance helps cover damages in the event of major security incidents.
A provider without insurance may not be prepared to handle serious breaches.
Evaluation Checklist for Choosing a Secure Provider
Businesses planning to launch a white-label Chewy app should perform proper due diligence before selecting a provider.
Questions to Ask Providers
- What security certifications does your platform follow?
- How is user data encrypted and stored?
- Do you conduct regular penetration testing?
- How often are security updates released?
- What monitoring systems detect cyber threats?
Documents to Request
Before signing an agreement, businesses should request:
- security architecture documentation
- compliance certification proof
- data protection policies
- incident response procedures
- service level agreements
These documents help verify the provider’s security capabilities.
Testing Procedures
Independent testing can help validate the platform’s security.
Recommended testing methods include:
- vulnerability scanning
- penetration testing
- API security testing
- performance stress testing
These tests help identify weaknesses before the app is launched.
Due Diligence Steps
A structured evaluation process should include:
- reviewing provider security certifications
- evaluating infrastructure architecture
- verifying compliance with privacy laws
- conducting independent security testing
- reviewing historical security incidents
Taking these steps significantly reduces the risk of launching an unsafe platform.
Best Practices for Secure White-Label Chewy App Implementation
Launching a secure white-label Chewy app requires careful planning before and after the platform goes live. Security should be integrated into every stage of development, deployment, and maintenance.
Businesses that follow structured security practices significantly reduce the chances of data breaches, compliance violations, and operational disruptions.
Pre-Launch Security Preparation
Security Audit Process
Before launching the app, a complete security audit should be conducted.
Security audits examine:
- backend infrastructure configuration
- application code security
- authentication systems
- API access controls
An independent security review helps identify vulnerabilities that internal teams may overlook.
Code Review Requirements
Secure code is the foundation of a safe ecommerce platform.
Professional development teams perform structured code reviews to detect:
- injection vulnerabilities
- authentication weaknesses
- insecure data handling practices
Code review processes also ensure developers follow secure coding standards.
Infrastructure Hardening
Infrastructure hardening reduces the attack surface of the platform.
This process includes:
- securing cloud servers
- restricting administrative access
- configuring firewalls properly
- disabling unnecessary services
A hardened infrastructure significantly improves platform resilience against cyberattacks.
Compliance Verification
Before launch, businesses must confirm that the platform meets all required compliance standards.
Verification typically includes:
- data privacy compliance checks
- payment security validation
- infrastructure security assessments
Proper compliance preparation helps avoid regulatory penalties.
Staff Security Training
Human error is one of the most common causes of security incidents.
Training programs should teach employees how to:
- recognize phishing attacks
- manage sensitive data securely
- use authentication systems properly
- follow internal security policies
Well-trained teams play an important role in protecting the platform.
Post-Launch Security Monitoring
Security does not stop after the app goes live. Continuous monitoring is essential to detect new threats and vulnerabilities.
Continuous Security Monitoring
Real-time monitoring systems track suspicious activities across the platform.
Monitoring tools detect:
- unusual login attempts
- suspicious transactions
- abnormal API requests
- bot traffic patterns
Early detection allows businesses to respond quickly before incidents escalate.
Regular Updates and Patches
Software components must be updated regularly to address newly discovered vulnerabilities.
Important updates include:
- framework security patches
- operating system updates
- dependency upgrades
- authentication improvements
Ignoring updates is one of the most common causes of security breaches.
Incident Response Planning
Every ecommerce platform should have a documented incident response plan.
A response plan defines:
- how security incidents are detected
- how teams respond to breaches
- how affected users are notified
- how systems are restored
Clear procedures reduce damage during a security event.
User Data Management
Secure data management policies protect user information throughout its lifecycle.
Best practices include:
- limiting internal access to sensitive data
- encrypting stored information
- implementing data retention policies
These measures help maintain regulatory compliance.
Backup and Recovery Systems
Data backup systems ensure that businesses can recover quickly after unexpected incidents.
Reliable systems include:
- automated encrypted backups
- geographically distributed storage
- disaster recovery procedures
Strong backup strategies protect both business continuity and customer data.
Security Implementation Timeline
| Stage | Key Security Activities |
|---|---|
| Planning Phase | Security architecture design and risk assessment |
| Development Phase | Secure coding practices and internal code reviews |
| Pre-Launch Phase | Security audits, penetration testing, and compliance checks |
| Launch Phase | Infrastructure monitoring and access control implementation |
| Post-Launch | Continuous monitoring, updates, and incident response planning |
Following these practices ensures that a white-label Chewy app remains secure throughout its lifecycle.
Security should always be treated as a continuous process rather than a one-time task.
Legal & Compliance Considerations
Security is not only a technical requirement. A white-label Chewy app must also comply with international data protection laws and ecommerce regulations. These laws protect users from misuse of personal data and ensure companies follow responsible business practices.
Ignoring legal requirements can lead to regulatory penalties, lawsuits, and loss of customer trust.
Regulatory Requirements
Data Protection Laws by Region
Different countries enforce different data protection regulations. Businesses operating globally must ensure their apps comply with the laws of each region where users are located.
Some major regulations include:
- GDPR in the European Union
- CCPA and CPRA in the United States
- Digital Personal Data Protection Act in India
- PIPEDA in Canada
These laws require companies to handle personal data responsibly and provide transparency about data usage.
Industry-Specific Regulations
Certain ecommerce platforms may fall under additional regulations depending on the services they offer.
For example:
- payment processing platforms must comply with PCI DSS
- veterinary service integrations may require healthcare data protections
- subscription commerce platforms must follow recurring billing regulations
Understanding industry-specific rules helps prevent legal complications.
User Consent Management
Modern privacy laws require explicit consent before collecting user data.
Apps must clearly inform users about:
- what data is being collected
- why the data is being collected
- how the data will be used
Consent mechanisms typically include cookie notices, privacy settings, and opt-in forms.
Privacy Policy Requirements
Every ecommerce app must provide a clear and transparent privacy policy.
A compliant privacy policy should explain:
- types of personal data collected
- how data is stored and protected
- whether data is shared with third parties
- how users can request data deletion
This document must be easily accessible inside the app and on the website.
Terms of Service Essentials
Terms of service define the legal relationship between the platform and its users.
Key elements include:
- user responsibilities
- acceptable platform usage
- payment and refund policies
- dispute resolution procedures
Clear terms protect businesses from legal disputes.
Liability Protection
Even with strong security measures, businesses must prepare for potential incidents. Legal safeguards help reduce financial and legal risks.
Insurance Requirements
Cyber liability insurance helps businesses manage the financial impact of data breaches.
Coverage may include:
- breach investigation costs
- legal defense expenses
- regulatory fines
- customer notification costs
Insurance is becoming a standard requirement for digital platforms.
Legal Disclaimers
Legal disclaimers clarify the responsibilities and limitations of the platform.
Disclaimers can address areas such as:
- product accuracy
- third-party integrations
- service interruptions
Proper disclaimers help reduce legal exposure.
User Agreements
User agreements establish rules for platform usage.
These agreements help address:
- fraudulent activity
- account misuse
- payment disputes
- intellectual property protection
Well-written agreements protect both users and businesses.
Incident Reporting Protocols
Regulations often require businesses to report security incidents within a specific timeframe.
For example:
- GDPR requires breach reporting within 72 hours
- several US regulations require rapid disclosure of data incidents
Businesses must maintain clear reporting procedures to meet these obligations.
Regulatory Compliance Monitoring
Compliance is not a one-time task. Regulations evolve frequently.
Companies must continuously monitor:
- new privacy laws
- changes in payment regulations
- international data transfer rules
Regular legal reviews ensure the app remains compliant.
Compliance Checklist by Region
| Region | Major Regulation | Key Requirements |
|---|---|---|
| European Union | GDPR | User consent, right to data deletion, breach reporting |
| United States | CCPA / CPRA | Consumer data rights, transparency in data usage |
| India | Digital Personal Data Protection Act | Responsible data processing and consent management |
| Canada | PIPEDA | Secure data storage and transparent privacy policies |
| Global Payments | PCI DSS | Secure handling of payment card information |
Meeting these requirements ensures that a white-label Chewy app operates legally and protects user privacy across different markets.
Why Miracuves White-Label Chewy App is Your Safest Choice
Choosing the right development partner plays a major role in the overall security of a white-label Chewy app. Miracuves focuses on building ecommerce platforms with security integrated into the architecture from the beginning.
This approach helps businesses launch scalable pet ecommerce apps while protecting user data, payment systems, and infrastructure.
Enterprise-Grade Security Architecture
Miracuves platforms are designed with a security-first architecture. The infrastructure is built to minimize vulnerabilities while supporting high traffic and complex ecommerce operations.
The architecture includes:
- secure cloud infrastructure
- protected server environments
- structured access control systems
- secure database management
These foundations reduce the risk of common cyberattacks.
Regular Security Audits and Certifications
Continuous auditing helps ensure the platform stays secure as technology evolves.
Miracuves conducts regular:
- vulnerability assessments
- penetration testing
- infrastructure security reviews
These audits help detect weaknesses early and maintain compliance with global security standards.
GDPR and CCPA Compliance by Default
Data protection laws require companies to handle personal information responsibly.
Miracuves white-label Chewy apps are built with privacy protections that support compliance with regulations such as:
- GDPR in Europe
- CCPA and CPRA in the United States
- other regional data protection laws
This helps businesses operate internationally without facing compliance risks.
24/7 Security Monitoring
Real-time monitoring helps detect suspicious activity across the platform.
Security monitoring systems analyze:
- login attempts
- payment activity
- API requests
- system performance patterns
Continuous monitoring allows security teams to respond quickly to potential threats.
Encrypted Data Transmission
All sensitive data transmitted through the platform is protected using strong encryption protocols.
This includes:
- user authentication data
- payment transactions
- order details
- personal customer information
Encryption prevents unauthorized interception of sensitive data.
Secure Payment Processing
Payment security is critical for ecommerce platforms.
Miracuves integrates secure payment systems that follow PCI DSS standards and use tokenized payment processing. This ensures that payment card details are never stored directly within the app infrastructure.
Regular Security Updates
Cybersecurity threats evolve constantly, which makes continuous updates essential.
Miracuves provides regular updates that include:
- vulnerability patches
- framework security improvements
- dependency upgrades
- infrastructure optimizations
Frequent updates help maintain strong protection against emerging threats.
Insurance Coverage Included
Cyber liability protection helps businesses manage risks associated with digital platforms.
Miracuves solutions include structured risk management and insurance support to protect businesses against potential security incidents.
Secure Your White-Label Chewy App with Miracuves
Security should never be treated as an optional feature when launching an ecommerce platform.
Miracuves builds white-label Chewy apps with enterprise-grade protection designed to safeguard businesses and their customers.
Our team has successfully delivered more than 9k+ projects while maintaining a strong record of platform stability and security.
Final Thought
Developing a white-label Chewy app can be a powerful opportunity for businesses entering the growing pet ecommerce market. However, success depends not only on features and design but also on the strength of the platform’s security foundation.
Modern ecommerce apps handle sensitive customer data, payment information, and subscription services. Without proper protection, these systems can become targets for cyberattacks and regulatory penalties. so let’s talk to Miracuves team today to request a security assessment and learn how to launch a secure, scalable pet ecommerce platform.
By choosing a security-focused development partner like Miracuves, companies can launch pet ecommerce platforms that meet modern compliance standards while delivering a reliable and protected user experience.
FAQs
1. How secure is a white-label Chewy app compared to custom development?
A white-label Chewy app can be just as secure as a custom-built platform if it follows modern security standards, strong encryption, and compliance certifications.
2. What happens if there is a security breach?
Businesses must activate an incident response plan, notify affected users, fix vulnerabilities, and report the breach according to regional regulations.
3. Who is responsible for security updates?
The platform provider usually manages core infrastructure updates, while the business must maintain operational security policies and user data practices.
4. How is user data protected in white-label apps?
User data is protected through encryption, secure servers, access control systems, and compliance with global privacy laws.
5. What compliance certifications should I look for?
Important certifications include ISO 27001, SOC 2 Type II, GDPR compliance, and PCI DSS for secure payment processing.
6. Can white-label apps meet enterprise security standards?
Yes. Many modern white-label platforms are built with enterprise-grade security architecture and infrastructure protections.
7. How often should security audits be conducted?
Security audits should be performed at least once or twice per year, along with continuous monitoring and vulnerability scanning.
8. What is included in Miracuves security protection?
Miracuves platforms include encrypted infrastructure, secure payment integrations, regular audits, compliance-ready architecture, and continuous monitoring.
9. How can security be managed across different countries?
Businesses must follow regional privacy laws, implement data protection policies, and ensure compliance with international regulations.
10. What insurance is recommended for app security?
Cyber liability insurance is recommended to cover financial risks related to data breaches, legal claims.
Related Articles