You’ve heard the horror stories about data breaches, stolen payment details, and marketplaces exposing user data.
When launching a resale marketplace like a white-label Vinted app, security quickly becomes the biggest concern for founders and investors.
In 2026, marketplace platforms handle massive amounts of sensitive data including user identities, payment details, shipping addresses, and messaging records. A single vulnerability can damage trust, trigger regulatory penalties, and cost millions.
This guide gives an honest look at white-label Vinted app security. You’ll learn the real risks, the security standards modern platforms must meet, and how businesses can launch safe, compliant marketplace apps.
More importantly, we’ll explain what separates a secure white-label solution from a risky one.
Understanding White-Label Vinted App Security Landscape
What “White-Label Security” Actually Means

White-label security refers to the security infrastructure, policies, and protections built into a ready-made application that businesses can rebrand and launch as their own marketplace.
In a white-label Vinted app, the core platform is pre-developed. However, the responsibility for protecting user data, transactions, and platform integrity must still meet modern cybersecurity standards.
A secure white-label marketplace should include:
- Secure backend infrastructure
- Encrypted user data storage
- Secure payment processing
- Continuous vulnerability monitoring
- Compliance with global data protection laws
If these elements are missing, the platform can become vulnerable to attacks.
Common Security Myths vs Reality
Many businesses assume white-label apps are automatically insecure. The reality is more nuanced.
| Myth | Reality |
|---|---|
| White-label apps are always less secure | Security depends on development standards and infrastructure |
| Only custom-built apps are safe | Many enterprise companies use secure white-label platforms |
| Small marketplaces are not targeted by hackers | Automated attacks target platforms of all sizes |
| Security can be added later | Security must be built into the architecture from day one |
The key difference is whether the provider follows enterprise-grade security practices.
Why Businesses Worry About White-Label Marketplace Apps
Entrepreneurs often worry about three main security areas when launching a resale marketplace.
- User data protection
- Payment security
- Platform abuse and fraud
Marketplace apps store large amounts of personal information including emails, phone numbers, addresses, and payment details. If this data is exposed, the consequences can be severe.
Trust is also a major factor. Buyers and sellers will only use a marketplace if they believe the platform is safe.
Current Threat Landscape for Resale Marketplace Platforms
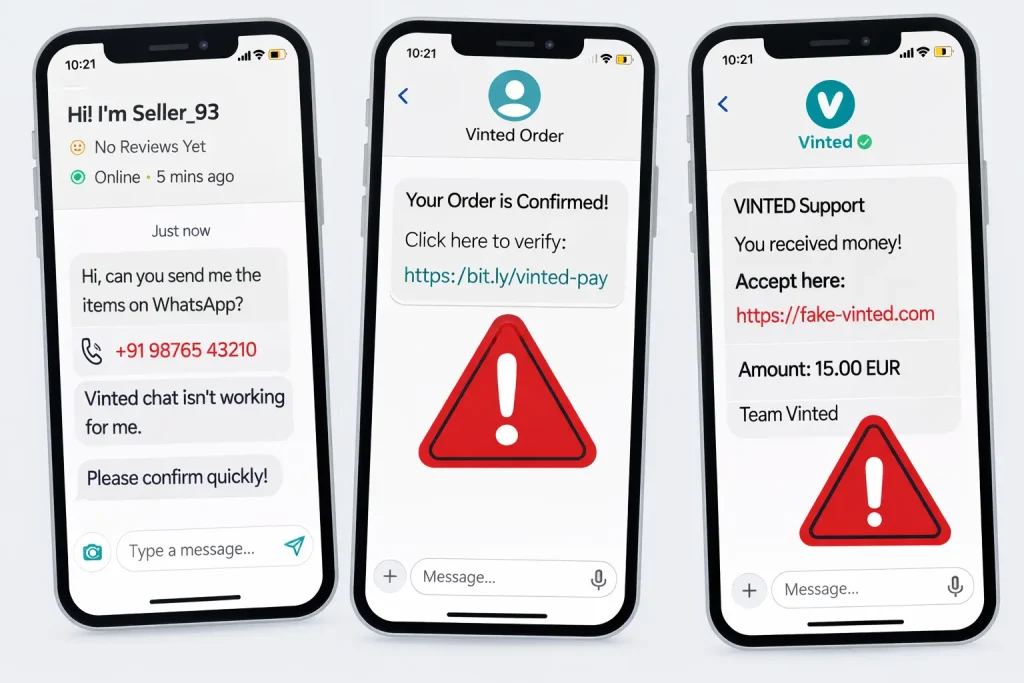
Marketplace apps like Vinted face several common cybersecurity threats.
- Account takeover attacks
- Fake seller scams
- Payment fraud
- API exploitation
- Data scraping
- Identity theft
Resale platforms are especially attractive to attackers because they combine financial transactions with personal data.
According to cybersecurity reports, e-commerce and marketplace platforms remain one of the top targets for cybercrime globally.
Security Standards Expected in 2026
By 2026, secure marketplace platforms are expected to implement advanced protection layers.
These include:
- End-to-end data encryption
- Zero-trust architecture
- Multi-factor authentication
- AI-based fraud detection
- Secure API gateways
- Real-time threat monitoring
Platforms that fail to implement these standards risk falling behind compliance and security expectations.
Real-World App Security Statistics
Recent cybersecurity research highlights the growing risk landscape for mobile apps and marketplaces.
- Over 43% of cyberattacks target small and medium businesses
- Nearly 60% of companies shut down within 6 months after a major data breach
- Mobile apps account for over 70% of digital fraud attempts in marketplace ecosystems
- Data breaches cost businesses an average of $4.45 million globally
These numbers show why security is no longer optional when launching a marketplace app.
Key Security Risks & How to Identify Them
Data Protection & Privacy Risks
Marketplace apps like a Vinted-style resale platform collect large volumes of personal and financial data. If this information is not properly protected, it becomes a prime target for cybercriminals.
User Personal Information
A resale marketplace stores sensitive user details such as:
- Full names
- Email addresses
- Phone numbers
- Shipping addresses
- User messages
If database security is weak, attackers may access or leak this information. This can lead to identity theft, fraud, and legal consequences.
Strong encryption and secure database architecture are essential to prevent unauthorized access.
Payment Data Security
A Vinted-style app processes payments between buyers and sellers. This includes credit cards, digital wallets, and escrow payments.
Without secure payment infrastructure, the risks include:
- Card data theft
- Transaction manipulation
- Fraudulent refunds
- Payment interception
Secure payment gateways and PCI DSS compliance are necessary to protect financial transactions.
Location Tracking Concerns
Marketplace apps often require location data to help users find nearby sellers or calculate shipping.
However, improper handling of location data can expose users to privacy violations.
Security protections should include:
- Limited location storage
- Encrypted data transmission
- User consent management
- Clear privacy settings
GDPR and CCPA Compliance
Data protection regulations have become stricter worldwide. Platforms must ensure compliance with privacy laws.
Key compliance requirements include:
- User consent for data collection
- Data deletion rights
- Transparent privacy policies
- Secure data storage practices
Failure to comply can result in heavy fines and legal action.
Technical Vulnerabilities
Even well-designed apps can suffer from technical security flaws if proper development standards are not followed.
Code Quality Issues
Poorly written code can introduce vulnerabilities such as:
- SQL injection
- Cross-site scripting (XSS)
- Authentication bypass
- Data exposure bugs
Secure development practices and regular code audits help prevent these problems.
Server Security Gaps
Marketplace platforms rely heavily on cloud servers and backend infrastructure.
Common server vulnerabilities include:
- Misconfigured cloud storage
- Weak firewall rules
- Unsecured admin panels
- Lack of server monitoring
Secure cloud architecture and access control systems are critical.
API Vulnerabilities
APIs connect the mobile app with the backend system.
If APIs are not properly secured, attackers can exploit them to access data or manipulate transactions.
Important API security measures include:
- Token-based authentication
- Rate limiting
- Input validation
- API gateway protection
Third-Party Integration Risks
Marketplace apps often integrate third-party services such as:
- Payment gateways
- Shipping services
- Analytics tools
- Notification systems
Each integration can introduce potential vulnerabilities if not carefully managed.
Business Risks
Security issues are not just technical problems. They can have serious business consequences.
Legal Liability
A data breach may expose the platform to lawsuits from users whose information was compromised.
Regulators can also impose fines for failing to protect customer data.
Reputation Damage
Trust is critical in resale marketplaces.
If users lose confidence in platform security, they may stop using the app completely.
Rebuilding reputation after a breach is extremely difficult.
Financial Losses
Security incidents can lead to multiple financial impacts:
- Fraudulent transactions
- Legal costs
- Compensation claims
- Infrastructure recovery expenses
For startups, these losses can be devastating.
Regulatory Penalties
Governments around the world are enforcing stricter cybersecurity regulations.
Companies that fail to protect user data may face significant penalties.
Examples include:
- GDPR fines up to 4% of global revenue
- Data protection penalties under CCPA
- Consumer protection enforcement actions
Risk Assessment Checklist
Businesses launching a white-label Vinted app should evaluate security risks before going live.
| Security Area | Key Question |
|---|---|
| Data Encryption | Is user data encrypted in transit and at rest? |
| Payment Security | Does the app comply with PCI DSS standards? |
| Authentication | Is multi-factor authentication implemented? |
| Server Infrastructure | Are cloud servers protected with strong access controls? |
| API Protection | Are APIs secured with authentication tokens and rate limits? |
| Compliance | Does the platform meet GDPR or regional privacy laws? |
| Monitoring | Is real-time threat detection enabled? |
Performing this assessment early helps prevent major vulnerabilities later.
Security Standards Your White-Label Vinted App Must Meet
Launching a resale marketplace in 2026 requires more than just a functional app. Security certifications and technical safeguards are now essential for protecting users and meeting regulatory expectations.
A secure white-label Vinted app must comply with both industry security certifications and technical protection standards.
Essential Security Certifications
Security certifications demonstrate that a platform follows internationally recognized data protection practices. Businesses should verify that their white-label provider supports these standards.
ISO 27001 Compliance
ISO 27001 is one of the most important global security certifications for information security management.
It ensures that the platform:
- Protects sensitive user data
- Maintains secure infrastructure policies
- Implements risk management procedures
- Regularly audits security controls
For marketplace platforms handling user identities and transactions, ISO 27001 compliance is a strong trust signal.
SOC 2 Type II Certification
SOC 2 Type II focuses on how companies manage customer data across five trust principles:
- Security
- Availability
- Processing integrity
- Confidentiality
- Privacy
A white-label marketplace provider with SOC 2 compliance demonstrates that its systems are continuously monitored and audited.
GDPR Compliance
If your marketplace has users in Europe, GDPR compliance is mandatory.
This regulation focuses on protecting personal data and giving users control over their information.
Key GDPR requirements include:
- Transparent data collection policies
- User consent management
- Data access and deletion rights
- Secure data processing practices
Failure to comply can result in heavy regulatory fines.
HIPAA Compliance (If Applicable)
HIPAA applies mainly to healthcare platforms. However, if your marketplace deals with medical products or health-related services, this regulation may apply.
HIPAA requires:
- Secure handling of health-related information
- Strict data access controls
- Encrypted data storage
PCI DSS for Payment Security
Payment Card Industry Data Security Standard (PCI DSS) is essential for any platform handling card payments.
A PCI DSS compliant marketplace ensures:
- Secure credit card transactions
- Protection against payment fraud
- Encrypted payment data
- Secure payment gateways
Without PCI compliance, the platform risks both fraud and legal penalties.
Technical Security Requirements
Certifications alone are not enough. Secure marketplace apps must also implement strong technical protection systems.
End-to-End Encryption
End-to-end encryption protects data during transmission between the user device and the server.
This ensures that sensitive information such as:
- Login credentials
- Payment details
- Private messages
cannot be intercepted by attackers.
Secure Authentication Systems
Weak login systems are one of the most common causes of account takeovers.
Secure marketplace apps should implement:
- Multi-factor authentication (2FA)
- OAuth authentication options
- Secure password hashing
- Login anomaly detection
These features reduce the risk of unauthorized account access.
Regular Security Audits
Security audits help identify vulnerabilities before attackers do.
Professional audits typically include:
- Code reviews
- Infrastructure testing
- Vulnerability scanning
- Compliance verification
Most enterprise platforms perform audits at least once or twice per year.
Penetration Testing
Penetration testing simulates real-world cyberattacks to find weaknesses in the system.
This process tests:
- Authentication systems
- Payment processing
- API security
- Server protection
Penetration tests should be conducted regularly, especially before major app updates.
SSL Certificates
SSL certificates encrypt communication between the user’s device and the platform servers.
Benefits include:
- Secure data transmission
- Protection against data interception
- Improved user trust
- Better search engine ranking signals
Every marketplace platform must use HTTPS with strong SSL encryption.
Secure API Design
APIs connect the mobile app, backend servers, and third-party services.
Secure API architecture should include:
- Token-based authentication
- Rate limiting to prevent abuse
- Input validation
- API gateway protection
- Monitoring for suspicious requests
Poor API security is one of the most common causes of data leaks in modern apps.
Security Standards Comparison
| Security Standard | Purpose | Why It Matters for a Vinted App |
|---|---|---|
| ISO 27001 | Information security management | Protects platform infrastructure and user data |
| SOC 2 Type II | Data security and operational integrity | Ensures continuous monitoring and auditing |
| GDPR | Personal data protection | Mandatory for European users |
| PCI DSS | Payment data security | Protects financial transactions |
| SSL/TLS Encryption | Secure data transmission | Prevents interception of sensitive information |
| Penetration Testing | Vulnerability discovery | Identifies weaknesses before attackers |
These standards form the foundation of a secure white-label marketplace platform.
Red Flags: How to Spot Unsafe White-Label Providers
Choosing the wrong white-label provider can expose your marketplace to serious security risks. Many businesses focus only on price or features and overlook critical safety factors.
Before selecting a provider for a Vinted-style marketplace app, it is important to identify warning signs that indicate weak security practices.
Major Warning Signs of Unsafe White-Label Providers
No Security Documentation
Reliable providers always maintain clear security documentation.
If a vendor cannot provide documents such as:
- Security architecture overview
- Data protection policies
- Compliance certificates
- Audit reports
it may indicate poor security practices.
Transparent documentation shows that security processes are properly implemented and maintained.
Suspiciously Cheap Pricing
Very low pricing can sometimes indicate compromised quality.
Secure apps require investments in:
- secure infrastructure
- security testing
- compliance certifications
- continuous monitoring
If a provider offers a full marketplace platform at extremely low cost without explanation, it may mean security has been ignored.
No Compliance Certifications
A professional white-label provider should support global security standards.
Missing certifications such as:
- ISO 27001
- SOC 2
- GDPR readiness
- PCI DSS support
is a major red flag for businesses planning to scale internationally.
Outdated Technology Stack
Technology evolves rapidly, and outdated systems can introduce vulnerabilities.
Older frameworks may lack modern security protections such as:
- modern encryption libraries
- secure authentication mechanisms
- advanced API protection
Always verify that the provider uses a modern and actively maintained technology stack.
Poor Code Quality
Weak code quality is one of the biggest sources of app vulnerabilities.
Signs of poor code practices include:
- frequent system crashes
- slow performance
- inconsistent functionality
- security bugs after updates
Professional providers conduct regular code reviews and security testing to maintain stability.
No Security Update Policy
Cyber threats evolve constantly. Without regular updates, an app quickly becomes vulnerable.
Unsafe providers often lack:
- patch management policies
- vulnerability monitoring
- scheduled security updates
A secure platform must release updates regularly to address new threats.
Lack of Data Backup Systems
Data loss can occur due to cyberattacks, server failures, or accidental deletion.
Secure providers implement:
- automated backups
- disaster recovery systems
- encrypted backup storage
Without backup infrastructure, recovery after a security incident becomes extremely difficult.
No Cybersecurity Insurance
Professional technology providers often maintain cybersecurity insurance.
Insurance helps cover financial damages in case of:
- data breaches
- service outages
- regulatory penalties
A provider without risk coverage may not be prepared for major security incidents.
Evaluation Checklist for Choosing a Secure Provider
Before selecting a white-label Vinted app provider, businesses should perform a structured security evaluation.
Important Questions to Ask Providers
- What security certifications does the platform support?
- How often are security audits performed?
- Is user data encrypted at rest and in transit?
- What payment security standards are implemented?
- How frequently are security updates released?
These questions reveal whether the provider prioritizes security.
Documents You Should Request
Requesting official documentation helps verify security claims.
Important documents include:
- compliance certificates
- penetration testing reports
- infrastructure security architecture
- data protection policies
- incident response procedures
If a provider refuses to share these materials, it is a strong warning sign.
Testing Procedures Before Launch
Before deploying the marketplace app, businesses should perform several security tests.
These include:
- vulnerability scanning
- penetration testing
- authentication security checks
- API security testing
Independent third-party testing adds an extra layer of protection.
Due Diligence Steps
A proper security evaluation typically involves the following steps:
- Verify security certifications
- Review the provider’s infrastructure security model
- Analyze previous client case studies
- Conduct independent security testing
- Evaluate the provider’s update and support policy
These steps significantly reduce the risk of launching an unsafe marketplace platform.
Best Practices for Secure White-Label Vinted App Implementation
Launching a secure resale marketplace requires planning both before launch and after deployment. Security must be integrated into the entire lifecycle of the app.
Businesses that treat security as an ongoing process are far less likely to face major data breaches or compliance issues.
Pre-Launch Security Measures
Before launching a white-label Vinted app, several critical security steps should be completed to ensure the platform is safe for users.
Security Audit Process
A comprehensive security audit helps identify vulnerabilities in the platform.
This process usually includes:
- infrastructure security analysis
- database protection review
- authentication system testing
- vulnerability scanning
Security audits should ideally be performed by independent cybersecurity specialists.
Code Review Requirements
Code review ensures the application is written according to secure development standards.
Developers should check for common vulnerabilities such as:
- SQL injection
- cross-site scripting (XSS)
- insecure authentication logic
- API access loopholes
A structured code review process reduces the chances of hidden security flaws.
Infrastructure Hardening
Infrastructure hardening strengthens the servers and cloud environment hosting the app.
Key measures include:
- configuring firewalls properly
- restricting admin access
- enabling intrusion detection systems
- securing cloud storage permissions
Proper infrastructure configuration prevents unauthorized access.
Compliance Verification
Before going live, the platform should be checked for regulatory compliance.
This includes verifying alignment with:
- GDPR data protection requirements
- payment security standards
- regional privacy laws
- marketplace consumer protection regulations
Compliance ensures the app can operate legally across different regions.
Staff Security Training
Human error remains one of the biggest causes of cybersecurity incidents.
Training internal teams helps reduce risks such as:
- phishing attacks
- credential misuse
- accidental data exposure
Security awareness programs should be conducted regularly.
Post-Launch Security Monitoring
Once the marketplace app is live, security must be continuously monitored and improved.
Ignoring post-launch security maintenance can quickly expose the platform to new threats.
Continuous Security Monitoring
Modern platforms use automated systems to detect suspicious behavior.
Monitoring tools help identify:
- unusual login attempts
- suspicious transactions
- abnormal traffic patterns
- potential data access violations
Early detection allows quick response before major damage occurs.
Regular Updates and Security Patches
Software vulnerabilities appear over time as new attack techniques emerge.
Secure platforms release regular updates that include:
- bug fixes
- vulnerability patches
- security improvements
Delaying updates increases the risk of exploitation.
Incident Response Planning
Even with strong security systems, incidents can still occur.
A clear incident response plan helps businesses react quickly.
This plan should include:
- breach detection procedures
- internal reporting protocols
- legal compliance actions
- user notification strategies
Preparation reduces the impact of security events.
User Data Management
Marketplace platforms must carefully manage how user data is stored and accessed.
Important practices include:
- encrypting sensitive user information
- limiting internal data access
- implementing data retention policies
- allowing users to manage their data preferences
Responsible data handling builds long-term user trust.
Backup and Recovery Systems
Reliable backup systems protect the platform from catastrophic data loss.
Secure platforms maintain:
- automated daily backups
- geographically distributed storage
- encrypted backup files
- tested recovery procedures
These systems ensure the marketplace can recover quickly after unexpected incidents.
Security Implementation Timeline
| Stage | Security Action | Purpose |
|---|---|---|
| Development Phase | Secure coding and architecture design | Prevent vulnerabilities from the start |
| Pre-Launch Testing | Security audits and penetration testing | Identify weaknesses before launch |
| Launch Stage | Infrastructure hardening and monitoring setup | Protect production environment |
| Post-Launch | Continuous monitoring and patch updates | Detect and prevent new threats |
| Long-Term Maintenance | Compliance audits and security reviews | Maintain trust and regulatory alignment |
A structured security implementation process ensures that the marketplace remains safe throughout its lifecycle.
Legal & Compliance Considerations
Launching a white-label Vinted app is not only a technical project. It also involves strict legal and regulatory responsibilities. Marketplace apps handle personal data, financial transactions, and communication between users, which means they must comply with multiple laws.
Ignoring legal compliance can result in fines, lawsuits, and platform shutdowns.
Regulatory Requirements
Different regions have their own regulations governing how apps collect, store, and process user data.
Data Protection Laws by Region
Modern apps must follow regional privacy regulations depending on where their users are located.
Some major global data protection laws include:
| Region | Regulation | Key Requirement |
|---|---|---|
| European Union | GDPR | User consent and strict personal data protection |
| United States | CCPA / CPRA | Consumer rights over personal data |
| United Kingdom | UK GDPR | Data protection and transparency rules |
| Canada | PIPEDA | Secure handling of personal information |
| India | Digital Personal Data Protection Act | Responsible data collection and storage |
If a marketplace app serves users across multiple regions, it must comply with several regulations simultaneously.
Industry-Specific Regulations
Some marketplaces may also face industry-specific compliance rules depending on their features.
Examples include:
- Payment regulations for digital transactions
- Consumer protection laws for marketplace platforms
- Anti-fraud and anti-money laundering regulations
- E-commerce taxation requirements
Understanding these requirements helps avoid legal complications later.
User Consent Management
Data protection laws require apps to obtain clear user consent before collecting personal information.
This means a marketplace app must provide:
- transparent consent forms
- clear data collection explanations
- user controls for privacy settings
- options to withdraw consent
Consent records should also be stored securely for compliance verification.
Privacy Policy Requirements
A privacy policy explains how the app collects, uses, and protects user data.
A proper policy should include:
- types of data collected
- purpose of data usage
- third-party data sharing details
- user rights regarding their data
- security protection measures
The policy must be easily accessible within the app.
Terms of Service Essentials
Terms of service define how users interact with the platform and each other.
For a resale marketplace, this should include:
- seller responsibilities
- buyer protection policies
- prohibited items or activities
- dispute resolution procedures
- account suspension rules
Clear policies help protect the platform from misuse.
Liability Protection
Legal protection is critical for marketplace businesses because they act as intermediaries between buyers and sellers.
Proper legal safeguards reduce exposure to lawsuits and financial damage.
Insurance Requirements
Many marketplace platforms maintain insurance coverage for potential risks.
Common insurance types include:
- cyber liability insurance
- data breach insurance
- professional liability insurance
- technology errors and omissions coverage
Insurance helps cover costs related to security incidents or legal claims.
Legal Disclaimers
Disclaimers clarify the platform’s responsibilities and limitations.
Typical marketplace disclaimers address:
- third-party seller liability
- transaction risks
- product authenticity responsibility
- shipping and delivery issues
These statements protect the platform from unfair liability.
User Agreements
Every marketplace app should require users to accept agreements before using the platform.
These agreements typically cover:
- acceptable platform behavior
- account responsibilities
- dispute handling procedures
- intellectual property rights
Digital acceptance records help enforce these agreements legally.
Incident Reporting Protocols
In many jurisdictions, companies must report data breaches within a specific timeframe.
For example:
- GDPR requires breach reporting within 72 hours
- Several U.S. states require immediate notification of affected users
Having a prepared reporting process helps businesses respond quickly.
Regulatory Compliance Monitoring
Compliance is not a one-time process. Regulations change frequently, and businesses must adapt.
Companies should regularly:
- review legal policies
- update privacy practices
- monitor regulatory changes
- conduct compliance audits
Continuous monitoring helps prevent legal violations.
Compliance Checklist by Region
| Compliance Area | EU (GDPR) | USA (CCPA/CPRA) | Global Best Practice |
|---|---|---|---|
| User Consent | Required | Required | Mandatory |
| Data Deletion Rights | Required | Required | Recommended |
| Data Encryption | Strongly recommended | Recommended | Essential |
| Breach Notification | Within 72 hours | State dependent | Immediate reporting |
| Privacy Policy Transparency | Mandatory | Mandatory | Essential |
Following these guidelines ensures that a white-label Vinted app operates legally and protects user rights.
Read more : – Business Model of Vinted : Complete Strategy Breakdown 2026
Why Miracuves White-Label Vinted App is Your Safest Choice
Security is one of the biggest concerns when launching a resale marketplace. Many ready-made platforms focus only on speed and features, but ignore long-term security and compliance.
Miracuves approaches white-label app development differently. The platform is designed with security-first architecture, ensuring that businesses can launch a marketplace app that protects users, transactions, and data.
Enterprise-Grade Security Architecture
Miracuves builds marketplace platforms using modern infrastructure designed to prevent common cyber threats.
Key architecture protections include:
- secure cloud infrastructure
- encrypted databases
- protected server environments
- role-based access control systems
This layered architecture significantly reduces the risk of unauthorized access.
Regular Security Audits and Certifications
Security is continuously tested and validated.
Miracuves performs:
- routine security audits
- vulnerability assessments
- infrastructure reviews
- penetration testing
Regular audits ensure that the platform stays protected against emerging cyber threats.
GDPR and CCPA Compliance by Default
Data protection regulations are becoming stricter worldwide. Miracuves platforms are designed to support modern compliance requirements.
Built-in compliance features include:
- user consent management
- secure data storage
- privacy control settings
- user data deletion mechanisms
This helps businesses operate safely across multiple regions.
24/7 Security Monitoring
Cyber threats can occur at any time. Continuous monitoring helps detect suspicious activity early.
Miracuves systems monitor:
- unusual login patterns
- abnormal transactions
- suspicious traffic activity
- potential system vulnerabilities
Early detection prevents small threats from becoming major incidents.
Encrypted Data Transmission
All sensitive data moving between users and servers is protected through strong encryption.
This ensures that:
- personal information remains private
- payment transactions stay secure
- user communication is protected
Encryption helps prevent data interception and unauthorized access.
Secure Payment Processing
Marketplace apps depend heavily on safe financial transactions.
Miracuves integrates secure payment systems that support:
- PCI DSS payment security standards
- trusted payment gateway integrations
- fraud monitoring systems
- secure escrow-based transactions
These features reduce the risk of financial fraud on the platform.
Regular Security Updates
Cybersecurity requires constant improvement. Miracuves maintains regular platform updates to address emerging threats.
Updates include:
- vulnerability patches
- security improvements
- performance optimizations
- technology upgrades
This ensures that the marketplace app remains secure as technology evolves.
Insurance Coverage and Risk Protection
To further protect businesses, Miracuves platforms are supported by strong risk management practices.
This includes infrastructure reliability measures and protection strategies designed to reduce operational risk and maintain platform stability.
Secure Marketplace Infrastructure Built for Growth
Security should not limit growth. Miracuves solutions are designed to scale while maintaining strong protection systems.
This allows businesses to safely grow their marketplace while maintaining trust with users.
Get a Secure Marketplace Platform with Miracuves
Security should never be compromised when launching a resale marketplace.
Businesses looking to launch a safe resale marketplace can talk to our team to understand how Miracuves protects platforms from modern cyber threats.
Final Thought
Launching a white-label Vinted app can be safe and scalable when security is treated as a priority from the start.
By choosing a provider that follows strong security standards, compliance regulations, and continuous monitoring, businesses can protect user data and build long-term trust.
A security-first platform like Miracuves helps ensure your marketplace is ready for the risks and regulations of 2026.
FAQs
1. Is a white-label Vinted app as secure as a custom-built platform?
Yes, a white-label Vinted app can achieve the same level of security as custom development when it is built with strong encryption, secure APIs, regular security audits, and recognized compliance standards.
2. What should be done if a security breach occurs?
If a breach happens, the system should immediately isolate the threat, secure the affected areas, inform impacted users, and follow all legal data breach reporting requirements.
3. Who handles security updates in a white-label marketplace app?
The platform provider usually manages the core infrastructure and security updates, while the business owner must ensure updates are applied and internal security practices are followed.
4. How is user data protected in a marketplace app like Vinted?
User information is protected through data encryption, secure servers, strict access control, and compliance with privacy laws such as GDPR.
5. Which compliance certifications should a marketplace app support?
A secure marketplace app should support certifications like ISO 27001, SOC 2 Type II, GDPR compliance, and PCI DSS for secure payment processing.
6. Can white-label apps meet enterprise-level security standards?
Yes, many modern white-label platforms are designed with enterprise-grade infrastructure and follow globally recognized cybersecurity frameworks.
7. How frequently should security audits be performed?
Security audits should generally be conducted at least once or twice a year, along with additional testing after major platform changes or updates.
8. What security features are included in Miracuves marketplace solutions?
Miracuves platforms include encrypted data transmission, secure payment integrations, compliance-ready architecture, and continuous security monitoring.
9. How can marketplace apps manage security across different countries?
Platforms must comply with regional data protection laws, implement proper user consent systems, and maintain clear privacy and data management policies.
10. What insurance coverage is recommended for app security?
Cyber liability insurance and data breach insurance are commonly recommended to help businesses manage financial risks related to cybersecurity incidents.
Related Articles