You’ve likely heard about data breaches, stolen payment data, and hacked marketplaces. For businesses planning to launch a sneaker resale marketplace like StockX, security is often the biggest concern.
In 2026, app security is essential. With the average global data breach costing around $4.45 million, marketplaces handling payments and personal data are major targets.
This guide explains the key security risks, compliance requirements, and best practices to build a secure sneaker marketplace. It also shows how solutions like Miracuves help businesses launch safe, compliant platforms from day one.
Understanding White-Label StockX App Security Landscape
What “White-Label Security” Actually Means
A white-label StockX app is a pre-built marketplace platform that businesses can rebrand and launch as their own sneaker resale marketplace.
Security in a white-label environment depends on three layers:
- Core platform security – protections built by the development provider
- Infrastructure security – hosting, servers, and cloud configuration
- Operational security – how the business manages users, data, and updates
If any of these layers are weak, the entire platform becomes vulnerable.
A well-built white-label StockX app should include enterprise-grade security architecture, encrypted databases, secure APIs, and regular vulnerability testing.
Without these protections, marketplaces that handle payments, authentication, and user data can become easy targets for attackers.
Common Security Myths vs Reality
Many businesses hesitate to launch a white-label marketplace because of misconceptions about security.
Security Myths vs Reality
| Myth | Reality |
|---|---|
| White-label apps are less secure than custom apps | Security depends on development quality and compliance standards |
| Hackers target only large companies | Small and mid-size platforms are targeted frequently |
| SSL certificates alone make apps secure | SSL is only one layer of security |
| White-label platforms cannot meet compliance standards | Many platforms meet ISO, SOC, and GDPR requirements |
In reality, poorly developed custom apps can be far more insecure than properly built white-label solutions.
Why People Worry About White-Label Apps
Marketplace apps like StockX involve multiple sensitive components.
These include:
- Payment transactions
- User authentication
- Order processing
- Personal user data
- Location tracking for shipping
Because these platforms manage both financial and identity data, businesses often worry about whether the platform is secure enough.
Another concern is shared codebases. Some believe vulnerabilities in one deployment may affect others.
However, professional providers isolate deployments using secure cloud architecture and dedicated infrastructure environments.
Current Threat Landscape for Sneaker Marketplace Platforms
Sneaker resale marketplaces have become high-value targets for cybercrime.
These platforms process high-value transactions, limited-edition products, and global payments.
The most common threats include:
- Payment fraud
- Account takeover attacks
- API abuse
- Bot-driven scalping systems
- Fake listing manipulation
- Data scraping
Many attackers use automated bots to exploit sneaker marketplaces.
These bots attempt to bypass authentication and manipulate listings or pricing.
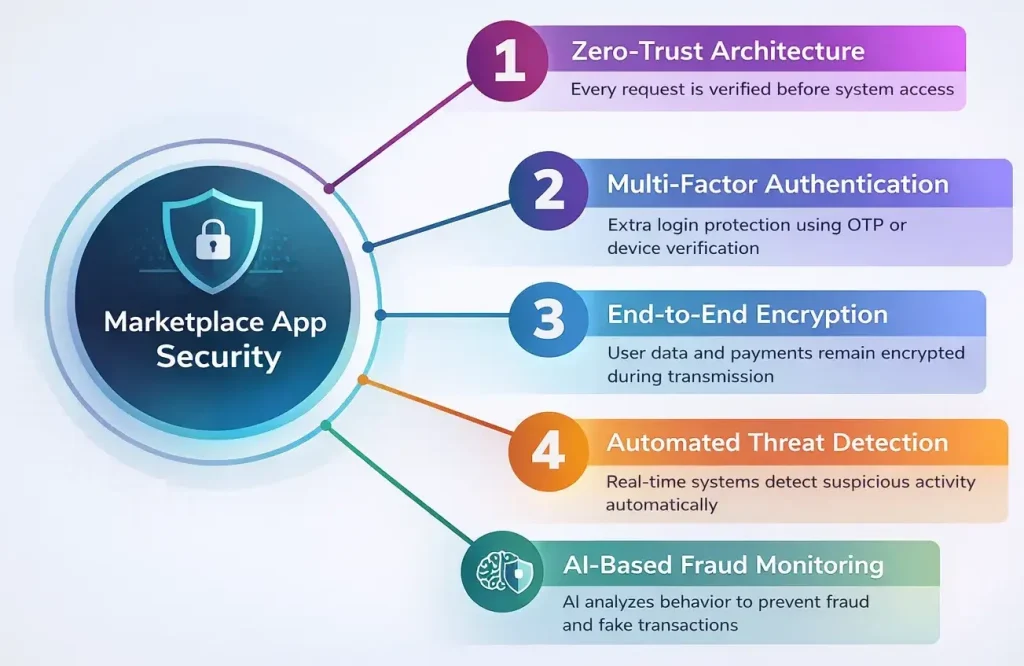
Security Standards for Marketplace Apps in 2026
Security expectations for marketplace platforms are significantly higher in 2026.
Modern sneaker resale platforms must implement:
- Zero-trust architecture
- Multi-factor authentication
- End-to-end encryption
- Automated threat detection
- AI-based fraud monitoring
Cloud providers such as AWS, Google Cloud, and Azure also require strict identity access management and secure API gateways.
Without these protections, platforms risk compliance violations and data exposure.
Real-World Statistics on App Security Incidents
Security research in 2026 shows how serious marketplace vulnerabilities can be.
Key findings include:
- 43% of cyberattacks target small and mid-sized businesses
- Application-layer attacks increased by over 30% globally
- More than 60% of breaches involve compromised credentials
- Marketplace platforms handling payments face higher fraud attempts
Sneaker resale platforms are particularly vulnerable because of high transaction values and competitive product releases.
That is why security must be built directly into the platform architecture, not added later as a patch.
Key Security Risks & How to Identify Them
Data Protection & Privacy Risks
Marketplace platforms like a StockX-style app collect sensitive user information. This includes personal data, payment details, and transaction history. If this data is not protected properly, it can lead to serious breaches and legal penalties.
User Personal Information
A StockX marketplace stores data such as:
- Full name
- Email address
- Phone number
- Shipping address
- Purchase history
If databases are not encrypted or access permissions are poorly configured, attackers may gain access to user identities.
Proper platforms should implement:
- Database encryption
- Role-based access control
- Secure identity verification systems
Payment Data Security
Payment processing is one of the highest risk areas for any marketplace.
If the platform does not follow PCI DSS standards, attackers may intercept payment information.
Secure implementations should include:
- Tokenized payment systems
- Secure payment gateways
- Fraud detection systems
- Encrypted payment transactions
Most secure marketplace apps never store raw card details directly.
Location Tracking Concerns
Marketplace platforms sometimes track location information for:
- Delivery verification
- Seller authentication
- Fraud detection
If location data is not protected, it can expose sensitive user behavior patterns.
Secure platforms should:
- Limit location storage duration
- Encrypt location data
- Use anonymized tracking where possible
GDPR and CCPA Compliance
Data privacy laws require businesses to handle user information responsibly.
For example:
- GDPR protects user data across Europe
- CCPA regulates consumer privacy in California
A marketplace app must include:
- User consent systems
- Data deletion requests
- Transparent privacy policies
- Secure data storage procedures
Failure to comply can result in severe financial penalties.
Technical Vulnerabilities
Technical weaknesses are one of the most common causes of security incidents in marketplace apps.
Code Quality Issues
Poorly written code can introduce vulnerabilities such as:
- SQL injection
- Cross-site scripting (XSS)
- Authentication bypass
- Session hijacking
Secure platforms rely on:
- Clean architecture
- Security-focused code reviews
- Automated vulnerability scanning
Server Security Gaps
Infrastructure misconfiguration can expose entire systems.
Common risks include:
- Open server ports
- Weak firewall rules
- Unpatched operating systems
- Insecure cloud storage
Secure deployments should implement:
- Cloud security policies
- Network isolation
- Regular server patching
API Vulnerabilities
APIs connect the mobile app, admin dashboard, and database.
If APIs are not secured, attackers may exploit them to access private data.
Secure API design includes:
- Authentication tokens
- Rate limiting
- API gateway protection
- Input validation
Third-Party Integrations
Many marketplace apps rely on external services such as:
- Payment gateways
- Shipping providers
- Analytics tools
- Authentication services
Each integration introduces a potential risk.
Providers must verify that third-party services meet modern security standards.
Business Risks
Security failures affect more than just technology. They also create major business consequences.
Legal Liability
If user data is exposed, companies may face lawsuits or regulatory investigations.
Many regions now require businesses to report breaches within strict time limits.
Reputation Damage
Marketplace trust is fragile.
Even a single breach can cause sellers and buyers to abandon the platform.
Trust recovery after a major incident can take years.
Financial Losses
Security incidents may lead to:
- Fraudulent transactions
- Chargebacks
- Regulatory fines
- Operational downtime
These costs often exceed the price of implementing strong security in the first place.
Regulatory Penalties
Failure to meet privacy regulations may result in large fines.
For example:
- GDPR penalties can reach 4% of global annual revenue
- Privacy violations can lead to government investigations
Risk Assessment Checklist
Businesses evaluating a white-label StockX app should review these security factors before launch.
This checklist helps identify potential weaknesses before they become real problems.
Security Standards Your White-Label StockX App Must Meet
Essential Certifications
Security certifications demonstrate that a platform follows globally recognized data protection and security practices. For a sneaker resale marketplace app, these certifications are critical for building trust and meeting legal requirements.
ISO 27001 Compliance
ISO 27001 is an international standard for information security management systems.
It ensures that a platform has:
- Risk assessment processes
- Secure data handling procedures
- Access control policies
- Continuous security monitoring
Platforms built with ISO 27001 practices follow strict guidelines for protecting sensitive user and business data.
SOC 2 Type II
SOC 2 Type II certification focuses on how a company manages data security over time.
It evaluates five trust principles:
- Security
- Availability
- Processing integrity
- Confidentiality
- Privacy
Marketplace platforms handling user accounts and financial transactions should operate under SOC 2 compliant infrastructure.
GDPR Compliance
The General Data Protection Regulation protects personal data of users within the European Union.
Marketplace apps must support:
- User consent management
- Data access requests
- Data deletion requests
- Transparent privacy policies
Any platform serving EU users must comply with GDPR to avoid major regulatory penalties.
HIPAA Compliance (If Applicable)
HIPAA applies mainly to healthcare data. It is typically not required for sneaker marketplaces.
However, understanding its security principles helps maintain strict data protection standards.
PCI DSS for Payment Security
Payment Card Industry Data Security Standard protects credit card transactions.
Marketplace apps handling payments must implement:
- Secure payment gateways
- Tokenized card storage
- Encrypted payment transmission
- Fraud monitoring systems
PCI DSS compliance significantly reduces the risk of payment data theft.
Technical Security Requirements
Even with certifications, technical security implementation is equally important.
End-to-End Encryption
End-to-end encryption ensures that sensitive information is protected during transmission.
Data protected by encryption includes:
- Login credentials
- Payment transactions
- User personal information
Strong encryption protocols prevent attackers from intercepting data.
Secure Authentication Systems
Authentication systems prevent unauthorized account access.
Secure marketplace apps implement:
- Two-factor authentication
- OAuth login systems
- Biometric authentication options
- Secure password policies
These measures significantly reduce account takeover attacks.
Regular Security Audits
Security audits identify vulnerabilities before attackers can exploit them.
Professional platforms conduct:
- Code audits
- Infrastructure audits
- Compliance checks
Audits should be performed multiple times each year.
Penetration Testing
Penetration testing simulates real-world cyberattacks to identify weaknesses.
Security specialists attempt to breach the system in controlled environments.
This process helps identify hidden vulnerabilities.
SSL Certificates
SSL certificates encrypt communication between users and the platform.
Every secure marketplace app must use HTTPS encryption across all pages.
Without SSL, attackers may intercept sensitive user data.
Secure API Design
APIs connect different components of the platform.
Secure APIs must include:
- Authentication tokens
- Rate limiting
- Data validation
- Access control rules
Poor API security is one of the most common causes of app breaches.
Security Standards Comparison
| Security Standard | Purpose | Why It Matters for a StockX App |
|---|---|---|
| ISO 27001 | Information security management | Protects platform infrastructure and data |
| SOC 2 Type II | Data security and privacy practices | Ensures reliable data handling |
| GDPR | User data privacy protection | Required for EU users |
| PCI DSS | Payment data protection | Secures financial transactions |
| SSL/TLS Encryption | Secure data transmission | Prevents interception attacks |
Meeting these standards ensures a marketplace app operates within modern cybersecurity and regulatory expectations in 2026.
Red Flags: How to Spot Unsafe White-Label Providers
Choosing the wrong white-label provider can expose your marketplace to serious security risks. Some vendors prioritize fast delivery and low pricing over proper security architecture.
Businesses should carefully evaluate providers before committing to a platform.
No Security Documentation
Reliable technology providers always maintain clear security documentation.
This includes:
- Security architecture details
- Data protection policies
- Compliance certifications
- Infrastructure documentation
If a provider cannot explain how the platform protects user data, it is a major warning sign.
Unusually Cheap Pricing
Extremely low development pricing often indicates shortcuts in security implementation.
Secure platforms require investment in:
- Security testing
- Secure infrastructure
- Compliance processes
- Continuous monitoring
If pricing seems unrealistic compared to the market, security may be compromised.
No Compliance Certifications
Professional platforms follow recognized compliance standards.
If a provider cannot demonstrate compliance with standards such as:
- ISO 27001
- SOC 2
- GDPR
- PCI DSS
then the platform may not meet modern security expectations.
Outdated Technology Stack
Older frameworks and unsupported technologies create vulnerabilities.
Unsafe providers often use:
- Outdated libraries
- Unsupported frameworks
- Legacy infrastructure
Modern platforms should use updated frameworks and actively maintained technologies.
Poor Code Quality
Low-quality code increases the risk of vulnerabilities.
Signs of poor development practices include:
- Lack of code reviews
- No security testing
- Inconsistent development practices
Professional platforms maintain strict code quality standards and automated testing pipelines.
No Security Update Policy
Security threats constantly evolve. Platforms must receive regular updates and patches.
If a provider does not offer ongoing security updates, vulnerabilities may remain exposed.
Businesses should confirm:
- Frequency of updates
- Patch management processes
- Security monitoring practices
Lack of Data Backup Systems
Data loss can be as damaging as a security breach.
Secure platforms maintain:
- Automated backups
- Redundant storage systems
- Disaster recovery plans
Without backups, data loss could permanently damage the platform.
No Cybersecurity Insurance
Some enterprise providers maintain cybersecurity insurance to cover potential breaches.
This coverage can help businesses recover from financial damages caused by security incidents.
While not mandatory, it shows that the provider takes risk management seriously.
Evaluation Checklist
Before selecting a white-label StockX app provider, businesses should perform proper due diligence.
Questions to Ask Providers
- What security certifications does the platform support?
- How often are security audits conducted?
- What encryption standards are used?
- How is payment data protected?
- How frequently are updates released?
Documents to Request
Businesses should request documentation such as:
- Security architecture overview
- Compliance certification reports
- Data protection policies
- Infrastructure security documentation
These documents help verify the provider’s claims.
Testing Procedures
Before launching the platform, companies should conduct independent testing.
Recommended tests include:
- Vulnerability scanning
- Penetration testing
- API security testing
- Infrastructure security assessment
Independent security reviews often reveal weaknesses that internal teams may overlook.
Due Diligence Steps
| Step | Purpose |
|---|---|
| Provider security review | Evaluate technical architecture |
| Compliance verification | Confirm regulatory readiness |
| Code audit | Identify development vulnerabilities |
| Infrastructure assessment | Verify server security |
| Independent penetration testing | Simulate real attack scenarios |
Careful evaluation during the selection stage can prevent costly security problems after launch.
Best Practices for Secure White-Label StockX App Implementation
Pre-Launch Security
Before launching a marketplace app, security must be implemented at every stage of development. Many security breaches occur because platforms skip proper preparation before going live.
Security Audit Process
A full security audit should be conducted before the platform launch.
This audit typically reviews:
- Source code vulnerabilities
- Infrastructure configuration
- Authentication systems
- Payment integrations
The goal is to detect weaknesses before attackers can exploit them.
Code Review Requirements
Professional platforms implement structured code review processes.
This includes:
- Peer code reviews
- Automated vulnerability scanning
- Secure coding practices
Code review helps identify common issues such as injection vulnerabilities and authentication flaws.
Infrastructure Hardening
Infrastructure hardening reduces the attack surface of the platform.
Important steps include:
- Restricting unnecessary server ports
- Implementing strong firewall rules
- Using secure cloud environments
- Applying system patches and updates
Secure infrastructure ensures attackers cannot easily access backend systems.
Compliance Verification
Before launching the app, businesses should verify that the platform meets required regulatory standards.
This includes checking compliance with:
- Data privacy laws
- Payment processing regulations
- Regional cybersecurity policies
Compliance verification helps prevent legal and financial risks.
Staff Security Training
Human error is a major cause of security incidents.
Employees managing the platform should be trained on:
- Secure password practices
- Phishing attack awareness
- Data protection procedures
- Incident reporting protocols
Security awareness training reduces internal risks.
Post-Launch Monitoring
Security responsibilities do not end after the app launch. Continuous monitoring is necessary to detect and respond to threats.
Continuous Security Monitoring
Real-time monitoring tools analyze platform activity and detect suspicious behavior.
Monitoring systems can identify:
- Unauthorized login attempts
- Unusual transaction patterns
- API abuse
- Potential bot attacks
Early detection allows teams to respond quickly to security incidents.
Regular Updates and Patches
Software vulnerabilities are discovered regularly.
Secure platforms release updates to fix security issues and maintain system stability.
Regular patch management helps prevent attackers from exploiting known vulnerabilities.
Incident Response Planning
Every platform should have a defined incident response plan.
This plan outlines how teams respond to:
- Data breaches
- Service disruptions
- Unauthorized system access
Quick response reduces the damage caused by security incidents.
User Data Management
User data must be handled with strict security practices.
Recommended practices include:
- Encrypting stored data
- Limiting internal data access
- Removing unnecessary data storage
Proper data management protects user privacy.
Backup and Recovery Systems
Reliable backup systems ensure the platform can recover from data loss or cyberattacks.
Backup strategies should include:
- Automated backups
- Off-site storage
- Disaster recovery testing
Strong recovery systems minimize downtime.
Security Implementation Timeline
| Phase | Security Focus |
|---|---|
| Development Stage | Secure coding and architecture design |
| Pre-Launch Stage | Security audits and compliance checks |
| Launch Stage | Infrastructure protection and monitoring setup |
| Post-Launch Stage | Continuous monitoring and security updates |
| Long-Term Operation | Regular audits and vulnerability testing |
Following these best practices helps ensure that a white-label StockX app operates securely and maintains user trust.
Legal & Compliance Considerations
Regulatory Requirements
Launching a StockX-style marketplace app involves strict legal responsibilities. Since the platform handles payments, personal data, and transactions between users, it must comply with multiple regional regulations.
Ignoring these requirements can lead to heavy fines, platform shutdowns, or legal disputes.
Data Protection Laws by Region
Different regions enforce different privacy regulations.
Some of the most important regulations include:
- GDPR in the European Union
- CCPA and CPRA in California
- Digital Personal Data Protection Act in India
- PIPEDA in Canada
- Privacy Act updates in Australia
These laws regulate how platforms collect, store, process, and delete personal user data.
Marketplace apps must implement proper user consent systems and transparent data handling policies.
Industry-Specific Regulations
Sneaker marketplaces operate within the broader eCommerce sector.
This means they must follow regulations related to:
- Online payments
- Consumer protection
- Fraud prevention
- Digital transactions
If the platform supports global sellers and buyers, additional international commerce regulations may apply.
User Consent Management
Privacy laws require platforms to clearly inform users how their data will be used.
Secure apps must include:
- Cookie consent banners
- Data collection notices
- Opt-in permission systems
Users should also have the ability to withdraw consent.
Privacy Policy Requirements
Every marketplace app must provide a transparent privacy policy.
This document should explain:
- What data is collected
- Why it is collected
- How it is stored
- How long it is retained
Clear privacy policies help businesses meet regulatory standards and build user trust.
Terms of Service Essentials
Terms of service protect the platform legally.
They define:
- Marketplace rules
- Seller responsibilities
- Buyer protections
- Dispute resolution processes
Well-written terms of service reduce legal disputes between users and the platform.
Liability Protection
Even with strong security measures, businesses must prepare for potential risks.
Legal protections help reduce financial and operational damage if incidents occur.
Insurance Requirements
Many marketplace operators purchase cybersecurity insurance.
This coverage can help manage costs related to:
- Data breaches
- Fraud incidents
- Legal investigations
- Business interruption
Insurance is becoming increasingly common for digital platforms.
Legal Disclaimers
Legal disclaimers clarify platform responsibilities.
For example, marketplaces often state that they act as intermediaries between buyers and sellers.
This helps limit liability in disputes involving counterfeit products or fraudulent listings.
User Agreements
User agreements should define acceptable platform behavior.
These agreements typically include:
- Account usage policies
- Listing requirements
- Payment rules
- Anti-fraud policies
Clear agreements reduce misuse of the platform.
Incident Reporting Protocols
Many regulations require companies to report data breaches quickly.
For example:
- GDPR requires breach notification within 72 hours
- Other regions may require immediate disclosure
Having a structured reporting process ensures compliance.
Regulatory Compliance Monitoring
Compliance is not a one-time process.
Laws evolve frequently, especially in areas such as data protection and digital commerce.
Businesses must regularly review:
- Privacy regulations
- Payment security standards
- Regional digital laws
Continuous monitoring ensures the platform remains legally compliant.
Compliance Checklist by Region
| Region | Key Regulations | Compliance Focus |
|---|---|---|
| European Union | GDPR | Data privacy and user rights |
| United States | CCPA, CPRA | Consumer data protection |
| India | Digital Personal Data Protection Act | Personal data security |
| Canada | PIPEDA | Data handling transparency |
| Australia | Privacy Act | Data protection and consent |
Following these legal and compliance requirements ensures that a StockX-style marketplace app operates safely and avoids regulatory penalties.
Read more : – Business Model of StockX : Complete Strategy Breakdown 2026
Why Miracuves White-Label StockX App is Your Safest Choice
Enterprise-Grade Security Architecture
Miracuves builds marketplace platforms using modern security architecture designed for high-transaction environments like sneaker resale marketplaces.
The platform includes secure backend infrastructure, encrypted data storage, and protected API communication layers. This architecture ensures that sensitive information such as user accounts and transactions remain protected.

Security is integrated at the development stage, not added later as an afterthought.
Regular Security Audits and Certifications
Security testing is performed regularly to identify potential vulnerabilities.
These audits include:
- Infrastructure security reviews
- Application vulnerability testing
- Compliance verification
Regular audits ensure the platform meets modern security expectations and reduces the risk of data breaches.
GDPR and CCPA Compliance by Default
Miracuves platforms are designed with privacy compliance built into the system.
This includes features such as:
- User consent management
- Data access requests
- Data deletion options
- Transparent data collection policies
These built-in tools help businesses comply with global privacy regulations without complex customization.
24/7 Security Monitoring
Continuous monitoring systems track suspicious activities across the platform.
Monitoring systems detect:
- Unauthorized login attempts
- Fraudulent transactions
- API misuse
- Bot-driven attacks
Real-time alerts allow teams to respond quickly to potential threats.
Encrypted Data Transmission
All data transmitted through the platform is protected using strong encryption protocols.
Encrypted communication protects:
- Login credentials
- Payment transactions
- Personal user data
Encryption ensures that attackers cannot intercept sensitive information.
Secure Payment Processing
Marketplace platforms must handle financial transactions safely.
Miracuves integrates secure payment systems that follow strict payment security standards.
Security measures include:
- Tokenized payment processing
- Secure payment gateways
- Fraud detection systems
These protections help reduce payment fraud and protect user financial data.
Regular Security Updates
Cybersecurity threats evolve constantly. Miracuves maintains ongoing update cycles to address new vulnerabilities.
Security updates include:
- Patch management
- Framework updates
- Security feature improvements
Regular updates ensure the platform remains protected against emerging threats.
Insurance Coverage for Risk Protection
Miracuves also supports risk mitigation strategies that help businesses prepare for unexpected security incidents.
Insurance-backed protection helps cover risks such as:
- Cybersecurity incidents
- Operational disruptions
- Legal claims related to security events
This additional layer of protection helps businesses operate with greater confidence.
Why Businesses Trust Miracuves
Miracuves has delivered 9k+ successful digital platforms across multiple industries, including marketplace solutions.
These platforms are designed with a strong focus on:
- Data protection
- Compliance readiness
- Secure infrastructure
- Reliable long-term support
This security-first approach helps businesses launch and scale their marketplaces safely.
Final Thought
More than 9k+ successful projects have been delivered without major security breaches, making Miracuves a trusted technology partner for secure digital platforms. Developing a StockX-style marketplace app is a powerful opportunity, but security must be a top priority. Platforms that handle payments, personal data, and high-value transactions require strong protection against modern cyber threats.
With the right technology partner, businesses can launch a secure, compliant marketplace that protects both users and revenue. Choosing a provider that prioritizes security architecture, compliance, and continuous monitoring makes all the difference. Businesses planning to develop a sneaker marketplace can talk to our team to evaluate platform risks and understand the safest way to build their marketplace.
FAQs
1. How secure is a white-label StockX app compared to custom development?
A professionally built white-label app can be just as secure as custom software if it follows modern security standards, encryption, and compliance requirements.
2. What happens if there is a security breach?
A secure platform should have an incident response plan, data recovery systems, and monitoring tools to quickly contain and resolve the issue.
3. Who is responsible for security updates?
The technology provider typically manages core platform updates, while the business ensures proper operational security practices.
4. How is user data protected in a white-label marketplace app?
User data is protected through encryption, secure authentication, access control systems, and compliance with privacy regulations.
5. What compliance certifications should I look for?
Important certifications include ISO 27001, SOC 2 Type II, GDPR compliance, and PCI DSS for payment security.
6. Can a white-label StockX app meet enterprise security standards?
Yes. Platforms built with modern infrastructure, encryption protocols, and security audits can meet enterprise-grade security standards.
7. How often should security audits be conducted?
Security audits should be conducted at least once or twice per year, along with continuous vulnerability monitoring.
8. What is included in the Miracuves security package?
Miracuves provides encrypted infrastructure, secure payment processing, compliance-ready architecture, and continuous monitoring systems.
9. How should security be handled for international users?
Platforms must follow regional data protection laws and implement global compliance frameworks to protect users across different countries.
10. What insurance is recommended for app security risks?
Cybersecurity insurance is recommended to cover potential losses related to data breaches, fraud incidents, and operational disruptions.
Related Articles