You have heard the horror stories about data breaches, leaked customer records, and payment fraud in eCommerce platforms. If you are planning to launch a white-label Zalando app, one question matters most: Is it truly safe?
In 2026, app security is not optional. With stricter GDPR enforcement, rising ransomware attacks, and growing consumer awareness about data privacy, even a minor security gap can damage your brand permanently.
This guide gives you an honest assessment of white-label Zalando app security, the real risks involved, and the exact standards your platform must meet. You will also learn how Miracuves ensures your investment is protected from day one with security-first development and compliance-driven architecture.
Understanding White-Label Zalando App Security Landscape
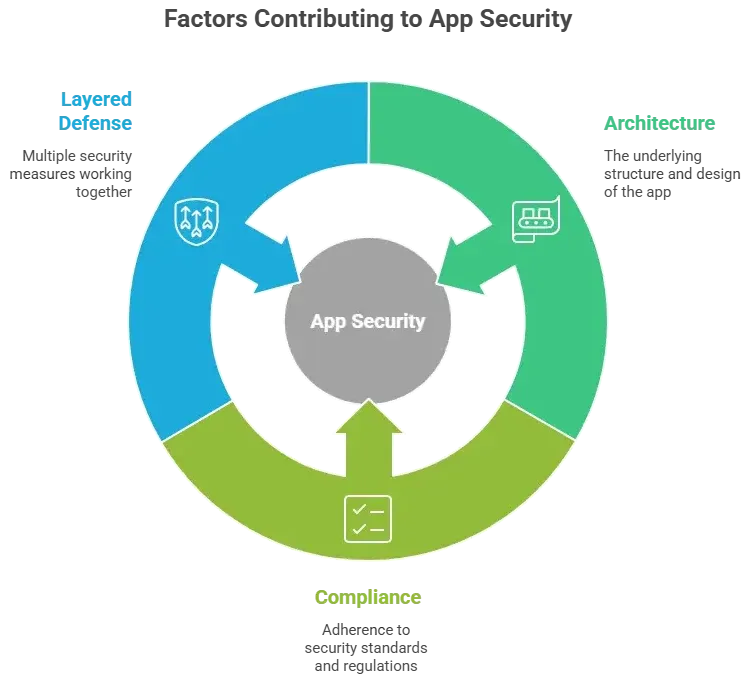
A white-label Zalando app is built on a reusable core framework customized for different businesses. Security depends on the base architecture, coding standards, hosting environment, and ongoing maintenance — not just branding changes.
If the core system is secure, every deployed app benefits. If it is weak, every version carries the same risk.
Why People Worry About White-Label Apps
- Shared codebase concerns
- Fear of hidden vulnerabilities
- Doubts about compliance readiness
- Payment and personal data exposure risks
These concerns are valid — especially in fashion eCommerce apps handling high transaction volumes.
Current Threat Landscape for Zalando-Type Platforms
Fashion marketplace apps face:
- Payment card fraud
- Account takeover attacks
- API exploitation
- Inventory manipulation bots
- Ransomware targeting cloud servers
According to recent cybersecurity industry reports, eCommerce platforms remain among the top three most targeted industries globally.
Security Standards in 2026
Modern white-label fashion apps must align with:
- Zero-trust architecture
- AI-based fraud detection
- Secure API-first development
- Continuous vulnerability scanning
- Cloud-native security controls
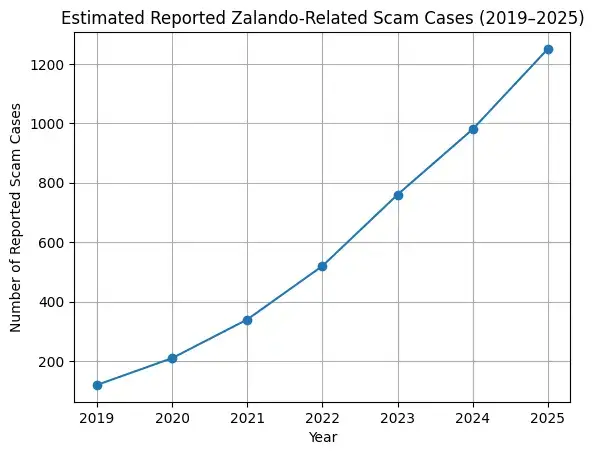
Real-World Statistics
- Global average cost of a data breach in 2025: over $4.4 million
- 60% of small businesses shut down within 6 months of a major cyberattack
- eCommerce fraud losses projected to exceed $48 billion globally in 2026
Security is not about fear. It is about preparation.
Suggested more : –Business Model of Zalando : Complete Strategy Breakdown 2025
Key Security Risks & How to Identify Them
Data Protection & Privacy Risks
User Personal Information
A white-label Zalando app collects names, addresses, phone numbers, and order history. If databases are not encrypted or access-controlled, this data becomes a prime target for attackers.
Payment Data Security
Without PCI DSS compliance, tokenization, and secure payment gateways, card data can be exposed. Payment breaches often lead to lawsuits and heavy fines.
Location Tracking Concerns
Fashion apps often use geolocation for delivery tracking and offers. Poorly secured APIs can expose user location data in real time.
GDPR / CCPA Compliance
Failure to implement consent management, data deletion rights, and transparent policies can result in penalties reaching millions under EU regulations.
Technical Vulnerabilities
Code Quality Issues
Poorly written or reused code without security review may contain SQL injection, XSS, or authentication flaws.
Server Security Gaps
Unpatched servers, weak firewall rules, and misconfigured cloud storage are common entry points for breaches.
API Vulnerabilities
Marketplace apps rely heavily on APIs. Weak authentication or exposed endpoints allow data scraping and account takeover attacks.
Third-Party Integrations
Payment gateways, logistics APIs, and analytics tools can introduce hidden vulnerabilities if not audited properly.
Business Risks
Legal Liability
Data leaks can lead to class-action lawsuits and regulatory investigations.
Reputation Damage
Fashion buyers lose trust quickly. One breach can permanently reduce user retention.
Financial Losses
Fraud refunds, downtime, legal fees, and recovery costs add up rapidly.
Regulatory Penalties
GDPR fines can reach 4% of global annual turnover.
Risk Assessment Checklist
- Is all user data encrypted at rest and in transit?
- Is the app PCI DSS compliant?
- Are APIs protected with OAuth 2.0 or similar protocols?
- Are regular penetration tests conducted?
- Is there a documented incident response plan?
- Are third-party vendors security-audited?
If you cannot confidently answer yes to these, your white-label Zalando app is at risk.
Security Standards Your White-Label Zalando App Must Meet
Essential Certifications
ISO 27001 Compliance
Ensures a structured Information Security Management System (ISMS). It proves your provider follows globally recognized risk management processes.
SOC 2 Type II
Validates that security controls are operational over time, not just documented. Critical for handling customer and financial data.
GDPR Compliance
Mandatory if serving EU users. Requires lawful data processing, user consent tracking, breach notification protocols, and right-to-erasure systems.
HIPAA (If Applicable)
Usually not required for fashion apps, but necessary if health-related wearable integrations are included.
PCI DSS for Payments
Non-negotiable for processing card payments. Covers encryption, secure storage, access control, and transaction monitoring.
Technical Requirements
End-to-End Encryption
All data must be encrypted in transit (TLS 1.3) and at rest (AES-256 or equivalent).
Secure Authentication
Multi-factor authentication, OAuth 2.0, biometric login support, and role-based access control are essential in 2026.
Regular Security Audits
Quarterly vulnerability assessments and annual third-party audits reduce risk exposure.
Penetration Testing
Ethical hackers should test the app at least once per year or after major updates.
SSL Certificates
Properly configured SSL with HSTS enforcement prevents downgrade and man-in-the-middle attacks.
Secure API Design
Rate limiting, API gateways, token validation, and zero-trust architecture protect backend systems.
Security Standards Comparison Table
| Standard | Required For | Why It Matters | Risk If Ignored |
|---|---|---|---|
| ISO 27001 | All serious platforms | Structured risk management | Operational security gaps |
| SOC 2 Type II | SaaS & eCommerce | Ongoing control validation | Trust loss with partners |
| GDPR | EU users | Legal data protection | Heavy regulatory fines |
| PCI DSS | Payment processing | Cardholder data security | Financial penalties & fraud |
| SSL/TLS 1.3 | All apps | Secure transmission | Data interception |
Meeting these standards is the minimum requirement for a safe white-label Zalando app in 2026.
Red Flags: How to Spot Unsafe White-Label Providers
No Security Documentation
If a provider cannot share security architecture details, audit reports, or compliance documents, that is a serious concern.
Cheap Pricing Without Explanation
Enterprise-grade security infrastructure is expensive. Extremely low pricing often means corners are being cut.
No Compliance Certifications
Lack of ISO 27001, SOC 2, or PCI DSS alignment signals weak internal controls.
Outdated Technology Stack
Old frameworks, unsupported libraries, and legacy hosting increase vulnerability exposure.
Poor Code Quality
No documented code review process or version control practices can lead to hidden security flaws.
No Security Updates Policy
If updates are irregular or reactive only after incidents, your app remains exposed.
Lack of Data Backup Systems
Without automated encrypted backups, recovery after ransomware becomes nearly impossible.
No Insurance Coverage
Professional cyber liability insurance reflects maturity and accountability.
Evaluation Checklist
Questions to Ask Providers
- Are you ISO 27001 or SOC 2 certified?
- How often do you conduct penetration testing?
- What encryption standards do you use?
- Do you provide breach notification support?
- Is PCI DSS compliance included?
Documents to Request
- Latest audit reports
- Penetration testing summary
- Data processing agreement
- Incident response policy
- Infrastructure architecture overview
Testing Procedures
- Conduct independent security testing before launch
- Review API security with third-party experts
- Verify compliance claims with certificates
Due Diligence Steps
- Check client case studies
- Review uptime and breach history
- Evaluate security SLA commitments
Choosing the wrong provider is the biggest security risk in any white-label Zalando app project.
Best Practices for Secure White-Label Zalando App Implementation
Security Audit Process
Conduct third-party vulnerability assessments and penetration testing before going live. Fix all critical and high-risk findings.
Code Review Requirements
Ensure structured peer reviews and automated static code analysis to eliminate injection flaws and authentication bugs.
Infrastructure Hardening
Use secure cloud configurations, firewall rules, intrusion detection systems, and zero-trust network access.
Compliance Verification
Confirm GDPR, PCI DSS, and regional data protection compliance before handling live user data.
Staff Training Programs
Train internal teams on phishing awareness, access control policies, and secure admin usage.
Post-Launch Monitoring
Continuous Security Monitoring
Deploy real-time threat detection, fraud monitoring, and log analysis tools.
Regular Updates and Patches
Apply security patches immediately. Outdated components are the leading cause of breaches.
Incident Response Planning
Maintain a documented response plan with defined roles, communication flow, and regulatory reporting timelines.
User Data Management
Implement strict role-based access, encryption key rotation, and automated data retention policies.
Backup and Recovery Systems
Use encrypted daily backups with tested disaster recovery procedures.
Security Implementation Timeline
Week 1–2: Security audit, compliance review, infrastructure setup
Week 3–4: Penetration testing and vulnerability fixes
Week 5: Final compliance verification and deployment hardening
Ongoing: Continuous monitoring, quarterly audits, annual penetration testing
Security is not a one-time setup. It is an ongoing operational discipline.
Legal & Compliance Considerations
Regulatory Requirements
Data Protection Laws by Region
- EU: GDPR requires lawful data processing, breach reporting within 72 hours, and user data rights management.
- USA: CCPA and CPRA mandate transparency, opt-out mechanisms, and data access rights.
- UK: UK GDPR mirrors EU standards with strict enforcement.
- India & APAC: Emerging data protection laws require data localization and consent controls.
Industry-Specific Regulations
If your Zalando-style app includes fintech services like wallet systems or BNPL, additional financial compliance rules may apply.
User Consent Management
Clear cookie banners, granular consent options, and stored consent logs are mandatory in most regions.
Privacy Policy Requirements
Must clearly explain data collection, storage duration, third-party sharing, and user rights.
Terms of Service Essentials
Define liability limitations, dispute resolution methods, refund policies, and user conduct standards.
Liability Protection
Insurance Requirements
Cyber liability insurance protects against breach costs, legal defense, and customer compensation claims.
Legal Disclaimers
Proper disclaimers reduce exposure in cases of misuse or third-party failures.
User Agreements
Well-drafted agreements define responsibility boundaries between platform, vendors, and users.
Incident Reporting Protocols
Have documented procedures aligned with regional laws for notifying authorities and users.
Regulatory Compliance Monitoring
Assign a compliance officer or partner with a provider that tracks evolving global regulations.
Compliance Checklist by Region
| Region | Key Regulation | Breach Reporting Time | Major Penalty Risk |
|---|---|---|---|
| EU | GDPR | 72 hours | Up to 4% global revenue |
| USA | CCPA/CPRA | Varies by state | Civil penalties & lawsuits |
| UK | UK GDPR | 72 hours | Significant financial fines |
| APAC | Varies by country | Varies | Increasing enforcement |
Ignoring compliance is not just risky — it is financially dangerous.
Why Miracuves White-Label Zalando App is Your Safest Choice
Miracuves Security Advantages
Enterprise-Grade Security Architecture
Built on secure, scalable cloud infrastructure with zero-trust network principles and hardened environments.
Regular Security Audits and Certifications
Continuous internal audits supported by industry-standard compliance alignment including ISO-based security practices.
GDPR / CCPA Compliant by Default
Privacy-by-design architecture ensures consent management, user data control, and regulatory readiness from day one.
24/7 Security Monitoring
Real-time monitoring systems detect unusual activity, fraud attempts, and intrusion patterns instantly.
Encrypted Data Transmission
TLS 1.3 encryption in transit and strong AES-based encryption at rest safeguard sensitive information.
Secure Payment Processing
PCI DSS-aligned payment gateway integration with tokenization to protect cardholder data.
Regular Security Updates
Scheduled patches, vulnerability scans, and proactive threat mitigation reduce long-term risk.
Insurance Coverage Included
Cyber liability structured support adds an extra layer of business protection.
Final Thought
Do not compromise on security. Miracuves white-label Zalando app solutions come with enterprise-grade security built in. Our 9k+ successful projects have maintained zero major security breaches. Talk to Our Security Experts Now and see why businesses trust Miracuves for safe, compliant platforms.
Launching a white-label Zalando app is a powerful business move, but security determines whether it becomes a long-term asset or a liability.
FAQs
1. How secure is white-label vs custom development?
Security depends on standards, not model. A properly built white-label Zalando app with ISO, SOC 2, and PCI compliance can be as secure as — or even more secure than — custom development.
2. What happens if there is a security breach?
You must activate your incident response plan, notify authorities (within 72 hours under GDPR if applicable), inform users, and start remediation immediately.
3. Who is responsible for security updates?
Primary responsibility lies with the technology provider. However, business owners must ensure updates are applied consistently.
4. How is user data protected in white-label apps?
Through encryption (TLS 1.3 in transit, AES-256 at rest), access control, tokenized payments, and continuous monitoring systems.
5. What compliance certifications should I look for?
ISO 27001, SOC 2 Type II, GDPR alignment, and PCI DSS for payment-enabled apps.
6. Can white-label apps meet enterprise security standards?
Yes, if built with secure architecture, audited regularly, and maintained with structured compliance controls.
7. How often should security audits be conducted?
Quarterly vulnerability scans and annual penetration testing are recommended minimum standards.
8. What is included in Miracuves security package?
Encrypted infrastructure, compliance-ready architecture, secure payments, monitoring, regular updates, and structured risk management support.
9. How to handle security in different countries?
Implement region-specific compliance controls such as GDPR (EU), CCPA (USA), and local data protection laws with proper consent tracking.
10. What insurance is needed for app security?
Cyber liability insurance covering breach response costs, legal defense, regulatory fines, and customer compensation.
Related Articles