
How Safe is a White-label Postmates App? Security Guide 2026
Key Takeaways What You’ll Learn White-label Postmates apps must protect customer data, real-time delivery tracking, merchant operations, and payment flows. Security in 2025 is not
Ready to Deploy
Our Readymade Solutions are built to execute your business idea into a successful growth story in no time.
Lets Do IT
Our IT Services are designed for immediate implementation—empowering your business with proven expertise, streamlined processes, and rapid results to drive your growth from day one.

Simplifying IT
for a complex world.
Learn about of Partnership Programs and our Certifications.
Nothing less than wonderful is what we do and what people have to say.
Be an expert or a novice, Join us and we will make a difference together.
Ready to Deploy
Our Readymade Solutions are built to execute your business idea into a successful growth story in no time.
Lets Do IT
Our IT Services are designed for immediate implementation—empowering your business with proven expertise, streamlined processes, and rapid results to drive your growth from day one.

Simplifying IT
for a complex world.
Learn about of Partnership Programs and our Certifications.
Nothing less than wonderful is what we do and what people have to say.
Be an expert or a novice, Join us and we will make a difference together.

Key Takeaways What You’ll Learn White-label Postmates apps must protect customer data, real-time delivery tracking, merchant operations, and payment flows. Security in 2025 is not

You’ve probably heard the horror stories—tenant data leaks, unauthorized access to rental records, payment information exposed, or property management apps getting hacked overnight. When you’re

Key Takeaways What You’ll Learn FedEx operates a logistics platform that relies on secure shipment tracking, routing, and real-time updates. Users track deliveries through apps
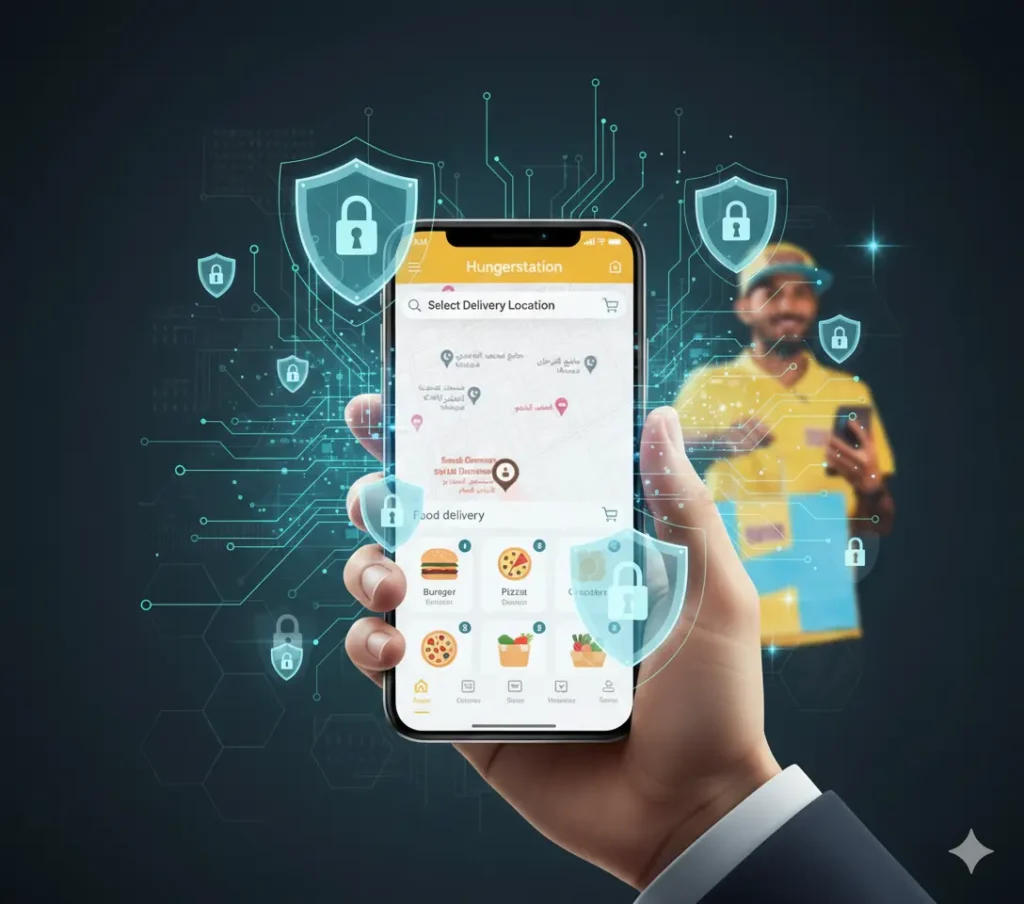
You’ve heard the horror stories about food-delivery apps leaking customer data, exposing payment details, or getting hacked because of insecure development practices. And in 2025,

Key Takeaways What You’ll Learn Gojek uses multi-layer security to protect users, drivers, and transactions across its platform. Data encryption and authentication help secure sensitive

You’ve heard the horror stories — travel apps leaking customer data, compromised payment gateways, and users suddenly losing access to bookings they paid for. In
Build Your Branded App - Clone or Custom

Envision. Decide. Deploy.
With Perfection in Just 6 Days
90+ readymade clone apps deployed in 6 days. Schedule a Live Walkthrough Now.
Custom development from 15 days. Free consultation