You’ve heard the horror stories about data breaches in eCommerce — leaked customer data, stolen card details, ransomware attacks freezing entire retail operations.
In 2026, fashion and retail apps like ASOS-style platforms are high-value targets. According to IBM’s 2024 Cost of a Data Breach Report, the global average cost of a data breach has reached $4.88 million. Retail remains one of the most targeted industries due to payment data, personal information, and high transaction volumes.
So if you’re planning to launch a white-label ASOS app, the critical question is:
Is it actually safe?
The truth is, white-label apps are not inherently unsafe — but their security depends entirely on architecture, compliance standards, infrastructure hardening, and ongoing monitoring.
In this guide, you’ll get:
- A realistic look at white-label ASOS app security in 2026
- The biggest risks facing eCommerce platforms
- Required compliance standards
- Practical evaluation checklists
- And how to choose a security-first development partner like Miracuves
Understanding White-Label ASOS Security Landscape
What “White-Label Security” Actually Means
A white-label ASOS app is a ready-made eCommerce framework customized with your branding, catalog, pricing model, and features.
But security is not about branding — it’s about:
- How the backend is architected
- Where the data is hosted
- How payment systems are integrated
- Whether compliance standards are built-in or optional
White-label security means the base product must already follow secure coding practices, encrypted data handling, secure API architecture, and regulatory compliance frameworks before customization even begins.
If security is “added later,” that’s a red flag.
Why People Worry About White-Label Apps
Business owners worry because:
- They don’t see the source code
- They don’t control infrastructure directly
- They fear shared vulnerabilities
- They are unsure about compliance documentation
These concerns are valid — especially if the provider lacks transparency.
Current Threat Landscape for ASOS-Type Platforms (2026)
Retail and fashion apps face specific threats:
- Card-not-present fraud
- Credential stuffing attacks
- API exploitation
- Fake return/refund abuse
- Bot-driven inventory scraping
- Ransomware targeting cloud databases
According to Mastercard’s 2024 fraud report, global eCommerce fraud losses are projected to exceed $48 billion annually by 2026.
Additionally, retail breaches frequently involve:
- Compromised admin dashboards
- Weak authentication systems
- Unpatched plugins or third-party integrations
Security Standards in 2026
In 2026, a secure white-label ASOS app must align with:
- ISO 27001 information security management
- SOC 2 Type II auditing
- GDPR and CCPA compliance
- PCI DSS 4.0 for payment security
- OWASP Top 10 vulnerability mitigation
Anything below these benchmarks is outdated.
Real-World Security Statistics
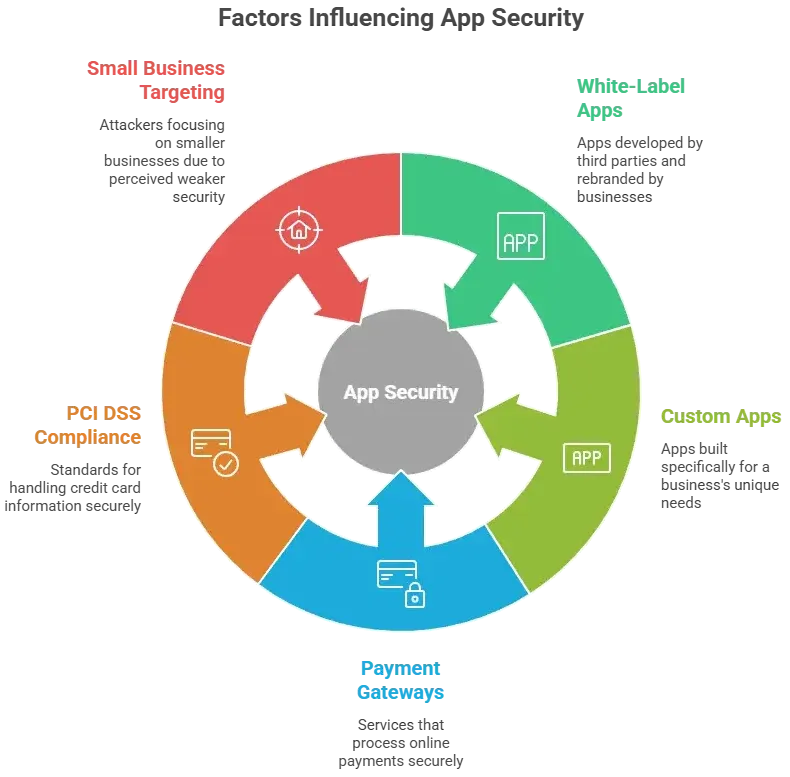
- 43% of cyberattacks target small and medium businesses (Verizon 2024)
- 60% of breached companies close within 6 months if recovery is weak
- Human error contributes to over 70% of breaches
- API-based attacks increased by over 20% year-over-year in 2024
For ASOS-style apps, APIs power everything — product catalogs, payments, tracking, personalization — making secure API design non-negotiable.
A white-label ASOS app can be secure — but only if its foundation is enterprise-grade.
Key Security Risks in a White-Label ASOS App & How to Identify Them
Launching a white-label ASOS app means handling sensitive customer data, financial transactions, and operational infrastructure. If security is weak in even one layer, the entire platform becomes vulnerable.
Let’s break down the highest-risk areas.
Data Protection & Privacy Risks
Fashion eCommerce apps collect extensive personal data. That makes them attractive to attackers.
User Personal Information
A white-label ASOS app stores:
- Names and addresses
- Phone numbers
- Email IDs
- Purchase history
- Behavioral tracking data
If encryption is not enforced at rest and in transit, this data can be exposed during breaches.
Payment Data Security
Even when using third-party gateways:
- Tokenization must be enabled
- No raw card data should be stored
- PCI DSS 4.0 standards must be followed
Misconfigured checkout APIs are one of the most common retail vulnerabilities.
Location Tracking Concerns
Many ASOS-style apps use:
- Geo-based promotions
- Delivery tracking
- IP-based personalization
If location data is improperly stored, it can create major GDPR violations.
GDPR & CCPA Compliance Gaps
Non-compliance can result in:
- GDPR fines up to €20 million or 4% of global annual turnover
- CCPA penalties up to $7,500 per intentional violation
Common compliance gaps:
- No user data deletion mechanism
- No consent management logs
- Weak privacy policy documentation
Technical Vulnerabilities
Code Quality Issues
Poorly structured code leads to:
- SQL injection risks
- Cross-site scripting (XSS)
- Authentication bypass flaws
Secure white-label providers follow OWASP Top 10 guidelines and conduct regular code reviews.
Server Security Gaps
Look for:
- Outdated server software
- Misconfigured cloud storage
- Weak firewall policies
- No intrusion detection system
Cloud misconfiguration remains one of the top causes of retail breaches in 2024–2026.
API Vulnerabilities
ASOS-style apps depend heavily on APIs. Risks include:
- Broken authentication
- Excessive data exposure
- Lack of rate limiting
- No API encryption
API attacks increased significantly in 2024 due to bot automation and AI-driven exploitation.
Third-Party Integration Risks
Fashion apps integrate:
- Payment gateways
- Logistics APIs
- CRM tools
- Marketing automation
Each integration expands the attack surface. Vendors must be vetted for SOC 2 or ISO compliance.
Business Risks
Security failure is not just technical — it’s financial and legal.
Legal Liability
Data breaches can trigger:
- Class-action lawsuits
- Regulatory investigations
- Mandatory breach notifications
Reputation Damage
Retail trust is fragile. A single breach can:
- Reduce customer lifetime value
- Increase churn
- Destroy brand credibility
Financial Losses
Costs include:
- Forensic investigations
- Legal fees
- Customer compensation
- Downtime losses
Average retail breach costs are among the highest across industries.
Regulatory Penalties
Failing audits or compliance checks can block expansion into certain regions, especially the EU and US markets.
White-Label ASOS App Risk Assessment Checklist
Use this quick evaluation framework:
Data Protection
- Is all user data encrypted at rest and in transit?
- Is there a documented GDPR compliance mechanism?
- Is data stored regionally when required?
Payments
- Is PCI DSS 4.0 compliance documented?
- Is tokenization implemented?
Infrastructure
- Are regular penetration tests conducted?
- Is there 24/7 monitoring?
- Are automated backups configured?
Authentication
- Is multi-factor authentication available?
- Are admin dashboards protected by IP restrictions?
Third Parties
- Are vendor security certifications verified?
- Is API traffic encrypted and rate-limited?
If multiple answers are unclear, the provider may not be security-ready.
Read more : – Best ASOS Clone Script 2025 – Launch Your Fashion Marketplace in Days
Security Standards Your White-Label ASOS App Must Meet
If a white-label ASOS app does not meet recognized global security standards in 2026, it is a liability — not an asset.
Here are the non-negotiable certifications and technical requirements your platform must comply with.
Essential Certifications
ISO 27001 Compliance
ISO 27001 ensures a structured Information Security Management System (ISMS).
It requires:
- Risk assessment documentation
- Asset management policies
- Access control frameworks
- Incident response planning
- Continuous monitoring
Without ISO 27001 alignment, security processes are usually inconsistent.
SOC 2 Type II
SOC 2 Type II validates how a company manages:
- Security
- Availability
- Processing integrity
- Confidentiality
- Privacy
Type II is critical because it audits security controls over time — not just at one point.
For white-label ASOS platforms handling large volumes of customer data, SOC 2 is a major trust signal.
GDPR Compliance
Mandatory for serving EU customers.
Requires:
- Explicit user consent
- Data minimization
- Right to access and delete data
- Data breach notification within 72 hours
Non-compliance can lead to fines up to 4% of global revenue.
HIPAA (If Applicable)
If your ASOS-style platform includes:
- Wellness integrations
- Health-related products with data capture
Then HIPAA compliance may apply in the U.S.
PCI DSS 4.0 (Critical for Payments)
As of 2024–2026, PCI DSS 4.0 is the required standard.
It mandates:
- Strong authentication controls
- Continuous security testing
- Network segmentation
- Strict cardholder data protection
If your provider says “we use Stripe so we’re compliant,” that is incomplete. The application layer must also comply.
Technical Security Requirements
Beyond certifications, technical safeguards must be built into the architecture.
End-to-End Encryption
- TLS 1.2 or higher
- AES-256 encryption for stored data
- Encrypted API communication
No sensitive data should ever travel unencrypted.
Secure Authentication
- Multi-factor authentication (2FA)
- OAuth 2.0 protocols
- Strong password policies
- Session timeout management
Admin dashboards must have stricter authentication controls.
Regular Security Audits
- Quarterly vulnerability scans
- Annual third-party penetration testing
- Automated code scanning
Retail apps are frequently targeted, so static security is not enough.
SSL Certificates
Every domain, subdomain, and API endpoint must:
- Use valid SSL certificates
- Enforce HTTPS
- Redirect HTTP traffic automatically
Secure API Design
Must include:
- Rate limiting
- Token-based authentication
- Minimal data exposure
- Logging and monitoring
Since ASOS-style apps are API-driven, insecure APIs are the fastest path to a breach.
Security Standards Comparison Table
| Security Standard | Purpose | Mandatory for ASOS App? | Risk if Missing |
|---|---|---|---|
| ISO 27001 | Information security management | Strongly Recommended | Poor security governance |
| SOC 2 Type II | Ongoing security validation | Highly Recommended | Low enterprise trust |
| GDPR | EU data protection | Mandatory (EU users) | Heavy fines |
| PCI DSS 4.0 | Payment data protection | Mandatory | Payment breaches |
| SSL/TLS | Data encryption | Mandatory | Data interception |
A secure white-label ASOS app in 2026 must meet both regulatory and technical standards. If even one layer is weak, attackers will exploit it.

Read more : – Business Model of ASOS : Complete Strategy Breakdown 2025
Red Flags: How to Spot Unsafe White-Label ASOS Providers
Not all white-label ASOS app providers prioritize security. Some focus only on speed and pricing — ignoring compliance, infrastructure hardening, and long-term risk.
Here’s how to identify unsafe providers before it’s too late.
Warning Signs You Should Never Ignore
No Security Documentation
If a provider cannot share:
- Security architecture overview
- Compliance certifications
- Data handling policies
- Incident response plan
That’s a major red flag.
Transparency is non-negotiable in 2026.
Cheap Pricing Without Explanation
Enterprise-grade security requires:
- Certified infrastructure
- Regular penetration testing
- Monitoring systems
- Compliance audits
If pricing is significantly below industry standards without justification, security corners are likely being cut.
No Compliance Certifications
If they lack:
- PCI DSS documentation
- GDPR readiness framework
- SOC 2 or ISO alignment
You carry the compliance liability — not them.
Outdated Technology Stack
Ask about:
- Framework version
- Server OS version
- Database security patches
- API authentication protocols
Outdated stacks are the leading cause of exploit-based attacks.
Poor Code Quality
Signs include:
- Slow app performance
- Frequent bugs
- No automated testing
- No version control transparency
Weak coding standards equal weak security.
No Security Updates Policy
Retail threats evolve constantly. If there’s:
- No patch management plan
- No update roadmap
- No vulnerability disclosure program
The platform will become outdated quickly.
Lack of Data Backup Systems
Essential requirements:
- Automated daily backups
- Encrypted backup storage
- Disaster recovery plan
- Recovery Time Objective (RTO) documentation
Without backups, ransomware can destroy your entire operation.
No Insurance Coverage
Serious providers carry:
- Cyber liability insurance
- Professional indemnity insurance
This protects you from shared risk exposure.
Evaluation Checklist Before Choosing a Provider
Use this due diligence framework:
Questions to Ask
- Are you PCI DSS 4.0 compliant?
- Do you conduct annual penetration testing?
- What encryption standards do you use?
- Where is customer data hosted?
- Do you support regional data storage for GDPR?
- How often are security patches applied?
Documents to Request
- Compliance certificates
- Security audit reports
- Data processing agreement (DPA)
- Incident response documentation
- SLA with uptime guarantees
Testing Procedures
Before launch:
- Request a staging penetration test
- Run vulnerability scans
- Test API endpoints
- Simulate failed login attempts
- Review admin access restrictions
Due Diligence Steps
- Verify hosting provider certifications
- Review third-party integrations
- Check public breach history
- Confirm backup restoration testing
- Review update frequency over the last 12 months
Choosing the wrong provider can expose your business to regulatory penalties, financial losses, and brand damage.
A security-first partner eliminates these risks from the foundation.
Best Practices for Secure White-Label ASOS App Implementation
Security is not a one-time setup. It is a lifecycle process that begins before launch and continues throughout the app’s operation.
Here’s how to implement security correctly.
Pre-Launch Security Measures
Security Audit Process
Before going live:
- Conduct third-party penetration testing
- Perform vulnerability assessment scans
- Review API endpoints for data exposure
- Validate encryption protocols
No white-label ASOS app should launch without a documented security audit report.
Code Review Requirements
Ensure:
- OWASP Top 10 vulnerabilities are mitigated
- Secure coding standards are followed
- Static code analysis tools are used
- Peer code reviews are documented
Retail platforms handle financial data, so code-level security is critical.
Infrastructure Hardening
Secure hosting must include:
- Firewall configuration
- Intrusion Detection & Prevention Systems (IDS/IPS)
- Network segmentation
- DDoS protection
- Role-based access controls
Cloud misconfiguration remains one of the leading causes of retail data exposure in 2024–2026.
Compliance Verification
Before accepting users:
- Confirm PCI DSS 4.0 readiness
- Validate GDPR consent mechanisms
- Review privacy policy alignment
- Ensure secure payment tokenization
Compliance should be validated, not assumed.
Staff Training Programs
Human error contributes to the majority of breaches.
Train your team on:
- Phishing detection
- Admin access management
- Password hygiene
- Incident reporting protocols
Security awareness reduces internal vulnerabilities.
Post-Launch Monitoring & Maintenance
Launching securely is only step one. Continuous monitoring is mandatory.
Continuous Security Monitoring
Must include:
- 24/7 server monitoring
- Real-time intrusion alerts
- Log monitoring
- API traffic analysis
Retail apps face automated bot attacks daily.
Regular Updates & Patches
- Apply security patches immediately
- Update dependencies monthly
- Retire outdated libraries
- Maintain version control documentation
Unpatched systems are the easiest entry point for attackers.
Incident Response Planning
Prepare for worst-case scenarios:
- Defined breach response workflow
- Legal notification procedure
- Customer communication template
- Forensic investigation partner
A fast response limits financial and reputational damage.
User Data Management
Implement:
- Automated data retention policies
- Secure deletion mechanisms
- Consent tracking logs
- Access request handling workflows
These are mandatory for GDPR and CCPA compliance.
Backup & Recovery Systems
Ensure:
- Daily encrypted backups
- Multi-region storage
- Tested disaster recovery process
- Recovery Time Objective under 24 hours
Backup without testing recovery is incomplete security.
Security Implementation Timeline
| Phase | Timeline | Key Activities |
|---|---|---|
| Planning | Week 1–2 | Risk assessment, compliance planning |
| Development | Week 3–8 | Secure coding, API hardening |
| Pre-Launch | Week 9–10 | Penetration testing, audit verification |
| Launch | Week 11 | Secure deployment, monitoring setup |
| Ongoing | Continuous | Patching, audits, compliance checks |
Security is not expensive — breaches are.
A properly implemented white-label ASOS app can operate at enterprise-grade safety levels when structured correctly from day one.
Legal & Compliance Considerations for White-Label ASOS Apps
Security is not just a technical responsibility. It is a legal obligation. In 2026, retail and fashion eCommerce apps operate under strict global data protection laws. Non-compliance can result in heavy penalties, forced shutdowns, and long-term brand damage.
Here’s what you must understand before launching.
Regulatory Requirements by Region
European Union – GDPR
If your white-label ASOS app serves EU customers, GDPR applies.
Key requirements:
- Explicit user consent before collecting personal data
- Right to access, modify, and delete data
- Data portability options
- Breach notification within 72 hours
- Appointment of a Data Protection Officer (if required)
Maximum penalty: Up to 4% of annual global turnover or €20 million, whichever is higher.
United States – CCPA & CPRA
For California users:
- Right to know what data is collected
- Right to opt-out of data sale
- Right to delete personal data
- Clear privacy disclosures
Other states (Texas, Virginia, Colorado, Florida) have enacted updated privacy laws effective 2024–2026, increasing compliance complexity.
United Kingdom – UK GDPR
Post-Brexit, UK GDPR remains aligned with EU data protection standards. Separate compliance documentation may be required.
India – Digital Personal Data Protection Act (DPDP Act 2023)
If operating in India:
- Clear user consent is mandatory
- Data fiduciaries must implement reasonable security safeguards
- Penalties can reach ₹250 crore for serious violations
Payment Regulations – PCI DSS 4.0
Mandatory worldwide if processing card payments.
Failure to comply can result in:
- Heavy fines
- Termination of payment gateway contracts
- Increased transaction fees
User Consent & Privacy Policy Requirements
A white-label ASOS app must include:
- Transparent privacy policy
- Cookie consent management
- Clear refund and data usage terms
- Terms of service agreement
- Opt-in marketing consent
Templates copied from the internet are not legally safe. Policies must reflect actual data practices.
Liability Protection Measures
Even with strong security, legal protection is essential.
Insurance Requirements
- Cyber liability insurance
- Data breach insurance
- Professional indemnity coverage
Retail apps without cyber insurance face extreme financial risk after breaches.
Legal Disclaimers & User Agreements
Your app must define:
- Data processing roles
- Limitation of liability
- Jurisdiction clauses
- Dispute resolution methods
Clear agreements reduce legal exposure.
Incident Reporting Protocols
Define:
- Who reports the breach
- Within what timeframe
- To which regulatory authority
- How customers are notified
Delay in reporting increases regulatory penalties.
Compliance Checklist by Region
| Region | Key Law | Data Consent Required | Breach Reporting Timeline |
|---|---|---|---|
| EU | GDPR | Explicit | 72 hours |
| UK | UK GDPR | Explicit | 72 hours |
| USA (CA) | CCPA/CPRA | Opt-out + disclosure | Without unreasonable delay |
| India | DPDP Act | Explicit | As prescribed by authority |
| Global Payments | PCI DSS 4.0 | Cardholder protection | Immediate containment required |
egal compliance is not optional for white-label ASOS apps. It must be built into architecture, documentation, and operational workflows from day one.
A security-first provider ensures compliance is embedded — not retrofitted.
Why Miracuves White-Label ASOS App is Your Safest Choice
Security is only as strong as the foundation it is built on. Many white-label providers treat security as an add-on. At Miracuves, it is the starting point.
When launching a white-label ASOS app, you need more than features and UI. You need enterprise-grade protection built directly into the architecture.
Here’s how Miracuves ensures maximum safety
Enterprise-Grade Security Architecture
Miracuves builds white-label ASOS platforms with:
- Secure cloud infrastructure
- Network-level firewalls and DDoS protection
- Role-based access control
- Hardened server environments
- Secure API gateways
Security is implemented at infrastructure, application, and data levels.
Regular Security Audits & Compliance Alignment
Miracuves platforms align with:
- PCI DSS 4.0 standards
- GDPR and CCPA compliance frameworks
- ISO-aligned security processes
- Secure coding practices based on OWASP guidelines
Regular vulnerability assessments and penetration testing ensure evolving threats are addressed proactively.
GDPR & CCPA Compliance by Default
Every Miracuves white-label ASOS app includes:
- Built-in consent management
- Data access and deletion workflows
- Secure user data storage
- Audit-ready documentation
Compliance is integrated into workflows, not added after launch.
24/7 Security Monitoring
Miracuves implements:
- Real-time server monitoring
- Intrusion detection systems
- Log analysis and alerting
- Continuous API monitoring
Threat detection happens before damage escalates.
Encrypted Data Transmission
All data is protected using:
- TLS-based encrypted communication
- Secure tokenized payment processing
- Encrypted backups
- Strict authentication protocols
No sensitive information is exposed in transit.
Secure Payment Processing
Miracuves ensures:
- PCI-compliant payment integrations
- Tokenization of card data
- Fraud detection mechanisms
- Secure checkout flows
Payment security is one of the most critical areas for fashion eCommerce apps.
Regular Security Updates
Security is an ongoing process.
Miracuves provides:
- Scheduled patch management
- Framework updates
- API security improvements
- Infrastructure upgrades
This prevents outdated vulnerabilities from being exploited.
Insurance Coverage & Risk Mitigation
Professional-grade protection includes:
- Risk management policies
- Secure development lifecycle
- Structured incident response processes
This reduces both operational and legal exposure.
Final Thought
Our 9k+ successful projects have maintained zero major security breaches. so Get a free security assessment and see why businesses trust Miracuves for safe, compliant platforms.
In 2026, launching a white-label ASOS app is not just about entering the fashion eCommerce market — it is about protecting customer trust. Retail platforms handle personal identities, payment data, and behavioral insights. One weak security layer can undo years of brand building.
FAQs
1. How secure is white-label vs custom development?
Security depends on implementation, not development type. A certified white-label ASOS app with PCI DSS, GDPR, and secure architecture can be safer than poorly built custom apps.
2. What happens if there’s a security breach?
You must activate an incident response plan, contain the breach, notify affected users, and report to authorities within required timelines (e.g., 72 hours under GDPR).
3. Who is responsible for security updates?
Both parties. The provider handles infrastructure and core updates, while the business must manage access control, policies, and internal processes.
4. How is user data protected in white-label apps?
Through encrypted storage (AES-256), TLS-secured transmission, role-based access controls, tokenized payments, and regular vulnerability testing.
5. What compliance certifications should I look for?
PCI DSS 4.0, GDPR compliance framework, SOC 2 Type II, and ISO 27001 alignment are essential for retail platforms.
6. Can white-label apps meet enterprise security standards?
Yes, if built with secure cloud infrastructure, audited code, penetration testing, and continuous monitoring systems.
7. How often should security audits be conducted?
Quarterly vulnerability scans and annual third-party penetration testing are recommended in 2026.
8. What’s included in Miracuves’ security package?
Secure architecture, encrypted data transmission, PCI-ready payments, GDPR workflows, 24/7 monitoring, and ongoing security updates.
9. How do you handle security in different countries?
By implementing region-specific compliance frameworks such as GDPR (EU), CCPA (USA), and DPDP Act (India), along with localized data handling policies.
10. What insurance is needed for app security?
Cyber liability insurance and data breach coverage are strongly recommended for financial risk protection.
Related Articles