You’ve heard the horror stories about data breaches, leaked customer details, and food delivery apps exposing payment information.
In 2026, food delivery platforms are prime targets for cybercriminals. They handle payments, store addresses, track live locations, and manage thousands of daily transactions. One small security gap can destroy brand trust overnight.
If you’re planning to launch a white-label EatNow app, safety should not be optional. It must be built into the architecture from day one.
In this guide, we’ll give you an honest assessment of white-label EatNow app security risks, compliance requirements, and practical steps to protect your business. We’ll also explain how choosing the right development partner—like Miracuves—can significantly reduce your exposure to security threats.
Understanding White-Label EatNow App Security Landscape

White-label EatNow app security refers to the protection framework built into a pre-developed food delivery platform that is customized under your brand.
Unlike fully custom-built apps, white-label platforms reuse a tested core system. Security depends on:
- How the base code is written
- Infrastructure configuration
- Compliance alignment
- Update management
- Hosting environment
A secure white-label EatNow app is not “less safe.” It is safe only if the provider follows enterprise-grade standards.
Common Security Myths vs Reality
| Myth | Reality |
|---|---|
| White-label apps are less secure than custom apps | Security depends on implementation, not model |
| Small food delivery platforms are not targeted | SMB platforms are increasingly targeted in 2026 |
| SSL certificate means fully secure | SSL protects transit, not database or APIs |
| Hosting on cloud means automatic safety | Misconfigured cloud systems cause major breaches |
Security failures usually happen due to poor configuration, not because the app is white-label.
Why People Worry About White-Label EatNow Apps
Food delivery apps collect sensitive data:
- Customer names and phone numbers
- Delivery addresses
- Real-time GPS location
- Credit/debit card details
- Restaurant payout information
If compromised, attackers can:
- Commit payment fraud
- Launch phishing attacks
- Steal customer databases
- Manipulate restaurant payouts
Trust is everything in food delivery. Once lost, recovery is expensive.
Current Threat Landscape for Food Delivery Platforms in 2026
The attack surface for EatNow-type platforms has expanded.
Key threats include:
- API attacks targeting order processing systems
- Credential stuffing using leaked passwords
- Payment gateway exploitation
- Ransomware targeting backend servers
- Supply chain attacks via third-party integrations
According to recent 2026 cybersecurity reports:
- Over 60% of mobile app breaches involve API vulnerabilities
- Food and retail apps remain among the top 5 most targeted sectors
- The average cost of a data breach globally has crossed $4.8 million
Food delivery platforms are attractive because they combine financial and location data.
Security Standards in 2026
Modern white-label EatNow apps must follow:
- Zero Trust Architecture
- Secure DevOps (DevSecOps)
- OWASP Mobile Top 10 compliance
- Mandatory encryption at rest and in transit
- Multi-factor authentication for admin access
- AI-driven threat detection systems
Without these, your platform is exposed.
A serious white-label provider designs security into the architecture, not as an afterthought.
Key Security Risks & How to Identify Them
Launching a white-label EatNow app without understanding risk exposure is dangerous. Food delivery platforms process high-volume transactions and sensitive user data daily.
Let’s break down the high-risk areas.
Data Protection & Privacy Risks
User Personal Information
Your EatNow app stores:
- Names
- Phone numbers
- Email addresses
- Delivery addresses
If databases are not encrypted properly, attackers can extract full customer profiles.
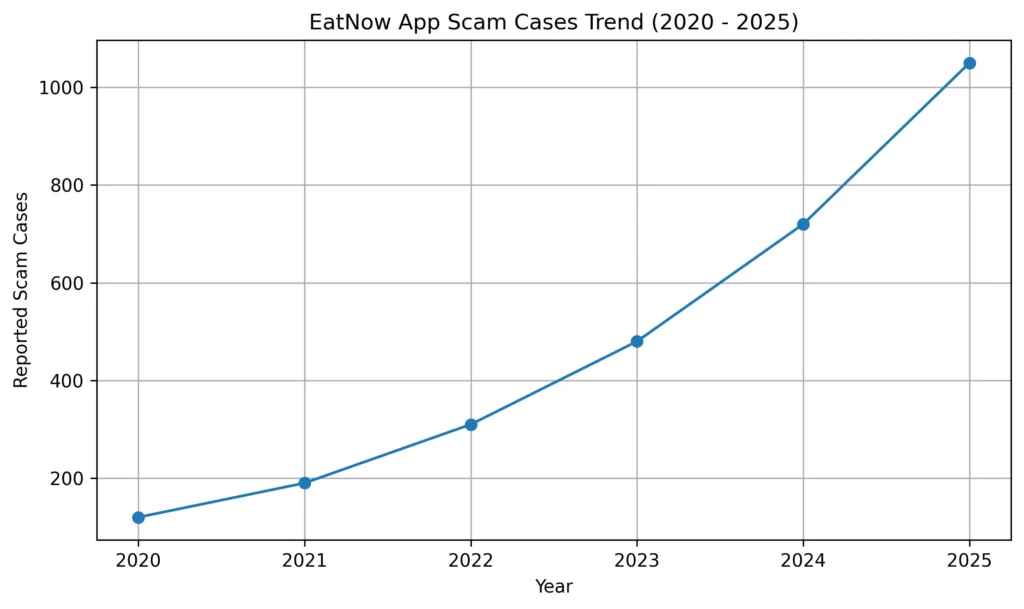
In 2026, data scraping and credential stuffing attacks have increased significantly across delivery apps.
Payment Data Security
Payment handling is the most sensitive area.
Risks include:
- Unsecured payment gateway integration
- Tokenization failures
- Man-in-the-middle attacks
- Stored card data without encryption
Without PCI DSS compliance, your business faces heavy penalties and potential shutdown.
Location Tracking Concerns
Real-time GPS tracking is essential for food delivery.
But it also creates risk:
- Location exposure
- Stalkerware exploitation
- API endpoint abuse
Location data must be encrypted both in transit and at rest.
GDPR / CCPA Compliance Issues
If your app serves EU or California users, strict privacy laws apply.
Non-compliance can lead to:
- Fines up to 4% of global annual revenue (GDPR)
- Statutory penalties under CCPA
- Legal action from users
Consent management and data deletion mechanisms must be built into the system.
Technical Vulnerabilities
Code Quality Issues
Poorly written or reused insecure code creates:
- Injection vulnerabilities
- Broken authentication
- Session hijacking
- Logic manipulation
A secure white-label EatNow app must follow OWASP Mobile Top 10 guidelines.
Server Security Gaps
Misconfigured servers are a common cause of breaches.
Typical issues:
- Open ports
- Weak firewall rules
- No intrusion detection
- Unpatched operating systems
Cloud does not mean secure by default.
API Vulnerabilities
Food delivery apps rely heavily on APIs.
Weak APIs can allow:
- Order manipulation
- Price tampering
- Unauthorized data access
- Admin privilege escalation
In 2026, API-based attacks account for more than half of mobile app security incidents.
Third-Party Integrations
Your app may integrate with:
- Payment gateways
- SMS providers
- Maps services
- Analytics tools
Each integration expands your attack surface.
Vendor risk assessment is critical.
Business Risks
Legal Liability
If a breach exposes user data, your company is legally accountable.
This includes:
- Regulatory fines
- Lawsuits
- Compensation claims
Reputation Damage
Customers lose trust quickly.
A single breach can:
- Reduce user retention
- Impact restaurant partnerships
- Lower investor confidence
Financial Losses
Costs include:
- Incident response
- Forensic investigation
- Legal defense
- Customer notification
- System rebuilding
The global average breach cost in 2026 exceeds $4.8 million.
Regulatory Penalties
Authorities now actively enforce digital compliance laws.
Non-compliance may result in:
- App store removal
- Operational bans
- Cross-border restrictions
White-Label EatNow App Risk Assessment Checklist
Use this quick evaluation list:
- Is all user data encrypted at rest and in transit?
- Is the payment system PCI DSS compliant?
- Are APIs tested against OWASP vulnerabilities?
- Is multi-factor authentication enabled for admin users?
- Are regular penetration tests conducted?
- Is there a documented incident response plan?
- Are backups automated and tested?
- Is GDPR/CCPA compliance documented?
- Is cloud infrastructure hardened and monitored?
- Are third-party vendors security audited?
If you answer “no” to more than two, your app is at serious risk.
Security is not optional in 2026. It is a competitive advantage.
Security Standards Your White-Label EatNow App Must Meet
In 2026, basic security is not enough. Your white-label EatNow app must meet globally recognized certifications and technical standards.
Without documented compliance, your platform is exposed legally and technically.
Essential Certifications
ISO 27001 Compliance
ISO 27001 ensures a structured Information Security Management System (ISMS).
It covers:
- Risk assessment frameworks
- Access control policies
- Incident response planning
- Continuous improvement
Serious white-label providers follow ISO-based processes even if formal certification is in progress.
SOC 2 Type II
SOC 2 Type II evaluates:
- Security
- Availability
- Processing integrity
- Confidentiality
- Privacy
This certification verifies that systems operate securely over time, not just at a single point.
GDPR Compliance
If serving European users, your EatNow app must:
- Collect explicit consent
- Provide data access rights
- Allow data deletion
- Implement privacy by design
Penalties can reach up to 4% of global turnover.
HIPAA (If Applicable)
If your food delivery platform connects with:
- Healthcare facilities
- Medical diet programs
- Hospital meal systems
HIPAA compliance may be required in the U.S.
PCI DSS for Payments
This is mandatory if you process card payments.
PCI DSS requires:
- Secure network configuration
- Encryption of cardholder data
- Access control measures
- Regular security testing
Without PCI compliance, payment processors may suspend your account.
Technical Security Requirements
Certifications alone are not enough. Technical implementation matters.
End-to-End Encryption
All sensitive data must be encrypted:
- HTTPS with TLS 1.3
- AES-256 encryption at rest
- Secure key management systems
Secure Authentication
Your EatNow app must include:
- Multi-factor authentication for admin users
- OAuth 2.0 or secure token-based authentication
- Strong password policies
- Session timeout controls
Regular Security Audits
Security audits should be conducted:
- Quarterly vulnerability scans
- Annual third-party audits
- Continuous code review
Penetration Testing
Ethical hackers simulate attacks to find weaknesses.
Pen testing should include:
- API security testing
- Mobile app testing
- Backend infrastructure testing
SSL Certificates
Valid SSL certificates are mandatory.
But remember, SSL protects data in transit only.
Secure API Design
APIs must include:
- Rate limiting
- Token validation
- Access control layers
- Input validation
- Logging and monitoring
Security Standards Comparison Table
| Security Requirement | Minimum Standard | Enterprise Standard (Recommended) |
|---|---|---|
| Data Encryption | HTTPS only | TLS 1.3 + AES-256 at rest |
| Payment Security | Basic gateway integration | PCI DSS Level 1 compliance |
| Authentication | Password-based | MFA + OAuth 2.0 |
| Security Testing | Annual scan | Quarterly audit + Pen testing |
| Compliance | Basic privacy policy | GDPR + SOC 2 + ISO framework |
| Monitoring | Manual checks | 24/7 real-time monitoring |
In 2026, enterprise-level security is becoming the baseline expectation, even for mid-sized food delivery platforms.
If your white-label EatNow app provider cannot demonstrate these standards, you are accepting unnecessary risk.
Red Flags: How to Spot Unsafe White-Label Providers
Not all white-label EatNow app providers follow secure development practices. Some focus only on speed and low cost.
That shortcut can cost you millions later.
Here are the warning signs.
Major Warning Signs
No Security Documentation
If a provider cannot share:
- Security architecture overview
- Compliance certificates
- Audit reports
- Data protection policies
That is a serious red flag.
Professional companies maintain documented security frameworks.
Cheap Pricing Without Explanation
If pricing is extremely low, ask why.
Security infrastructure requires:
- Secure cloud hosting
- Monitoring systems
- Regular audits
- Skilled engineers
If those costs are missing, security is likely compromised.
No Compliance Certifications
In 2026, any serious white-label EatNow app provider should align with:
- GDPR
- PCI DSS
- SOC 2
- ISO-based processes
If they dismiss compliance as “optional,” reconsider.
Outdated Technology Stack
Ask about:
- Backend framework versions
- Database security models
- Encryption protocols
If they use outdated libraries or unsupported frameworks, vulnerabilities are almost guaranteed.
Poor Code Quality
Signs include:
- Slow app performance
- Frequent crashes
- Inconsistent behavior
- Weak authentication flows
Code quality directly impacts security.
No Security Updates Policy
Ask:
- How often are security patches released?
- How are vulnerabilities disclosed?
- Is there a responsible disclosure program?
No update policy means your app will become vulnerable over time.
Lack of Data Backup Systems
Every secure EatNow app must have:
- Automated daily backups
- Encrypted storage
- Disaster recovery plans
Without backup systems, ransomware attacks can shut down operations.
No Insurance Coverage
Cyber liability insurance is becoming standard in 2026.
If a provider has no insurance, you may absorb full legal and financial damage.
White-Label EatNow App Provider Evaluation Checklist
Use this checklist before signing any contract.
Questions to Ask Providers
- Are you PCI DSS compliant?
- Do you follow OWASP Mobile Top 10 guidelines?
- How often do you conduct penetration testing?
- Is data encrypted at rest and in transit?
- Do you provide incident response support?
- What cloud security controls are implemented?
Documents to Request
- Compliance certificates
- Security audit reports
- Data processing agreement (DPA)
- Infrastructure architecture diagram
- Backup and disaster recovery documentation
Testing Procedures
Before launch:
- Conduct independent penetration testing
- Run API vulnerability scans
- Review admin access controls
- Test data deletion functionality
Due Diligence Steps
- Verify certification authenticity
- Check client references
- Review past security incidents
- Assess support responsiveness
- Evaluate DevSecOps practices
If a provider avoids detailed security conversations, that is your answer.
In 2026, transparency equals trust.
Best Practices for Secure White-Label EatNow App Implementation
Security is not just about choosing the right provider. It is about implementing the app correctly.
A secure launch reduces 70% of preventable risks.
Pre-Launch Security
Security Audit Process
Before going live:
- Perform vulnerability assessment
- Conduct penetration testing
- Review API security
- Test admin access controls
Independent third-party audits are strongly recommended.
Code Review Requirements
Ensure:
- Secure coding standards are followed
- No hardcoded credentials exist
- Input validation is properly implemented
- Authentication flows are tested
OWASP compliance must be verified.
Infrastructure Hardening
Your hosting environment must include:
- Firewall configuration
- Network segmentation
- Intrusion detection systems
- Secure cloud configuration
Misconfigured cloud storage remains one of the top breach causes in 2026.
Compliance Verification
Confirm alignment with:
- PCI DSS (for payments)
- GDPR / CCPA (for privacy)
- SOC 2 practices
- Regional data storage laws
Document everything.
Staff Training Programs
Human error causes a large percentage of breaches.
Train your team on:
- Phishing awareness
- Secure password management
- Access control policies
- Incident reporting procedures
Post-Launch Monitoring
Security does not stop after launch.
Continuous Security Monitoring
Implement:
- Real-time threat detection
- Log monitoring
- Suspicious login alerts
- API traffic analysis
24/7 monitoring reduces response time.
Regular Updates and Patches
Schedule:
- Monthly security patch reviews
- Immediate critical vulnerability fixes
- Dependency updates
Unpatched software is a common attack vector.
Incident Response Planning
Create a documented response plan covering:
- Breach identification
- Containment strategy
- User notification
- Legal reporting
- Recovery steps
Test this plan annually.
User Data Management
Maintain:
- Data retention policies
- Secure deletion mechanisms
- Encrypted storage systems
- Consent management logs
Backup and Recovery Systems
Best practice includes:
- Daily automated backups
- Encrypted backup storage
- Multi-region replication
- Quarterly recovery testing
White-Label EatNow App Security Implementation Timeline
| Phase | Timeline | Key Security Actions |
|---|---|---|
| Planning | Week 1–2 | Risk assessment, compliance mapping |
| Development | Week 3–8 | Secure coding, API hardening |
| Pre-Launch | Week 9–10 | Pen testing, audit verification |
| Launch | Week 11 | Monitoring activation, backup validation |
| Ongoing | Continuous | Monitoring, patching, compliance review |
In 2026, secure implementation is not a luxury. It is operational survival.
If your white-label EatNow app is not monitored continuously, it is only a matter of time before vulnerabilities are exploited.
Legal & Compliance Considerations
Launching a white-label EatNow app without legal compliance is risky. In 2026, regulators are stricter, and penalties are higher.
You must understand regional laws before operating.
Regulatory Requirements
Data Protection Laws by Region
Different regions enforce different privacy frameworks.
- European Union: GDPR requires explicit consent, data portability, and breach reporting within 72 hours.
- United States: CCPA (California), CPRA updates, and state-level privacy laws like Texas and Virginia privacy acts.
- Canada: PIPEDA compliance required for personal data handling.
- Australia: Privacy Act amendments increasing penalties for serious breaches.
- India: Digital Personal Data Protection Act enforcement strengthened in 2026.
If your EatNow app operates globally, compliance must be multi-layered.
Industry-Specific Regulations
Food delivery platforms may also need:
- Local food safety authority alignment
- Digital payment regulations
- Electronic transaction laws
- Consumer protection compliance
Ignoring industry-specific rules creates legal exposure.
User Consent Management
Your app must:
- Clearly request consent for data collection
- Allow users to withdraw consent
- Maintain consent logs
- Provide opt-out mechanisms
Consent cannot be hidden in complex terms.
Privacy Policy Requirements
Your privacy policy must clearly define:
- What data is collected
- Why it is collected
- How long it is stored
- Who it is shared with
- How users can request deletion
Transparency builds legal protection.
Terms of Service Essentials
Your terms must include:
- Limitation of liability
- Dispute resolution clauses
- Payment processing terms
- Refund and cancellation policies
- User conduct policies
Legal documentation must match actual system practices.
Liability Protection
Insurance Requirements
In 2026, most serious platforms carry:
- Cyber liability insurance
- Data breach response coverage
- Professional indemnity insurance
Insurance reduces financial exposure after incidents.
Legal Disclaimers
Your EatNow app should clearly state:
- Service limitations
- Third-party integration responsibilities
- Force majeure clauses
Disclaimers do not replace compliance, but they reduce risk.
User Agreements
Digital acceptance records must be stored securely.
This protects you in legal disputes.
Incident Reporting Protocols
If a breach occurs, you must:
- Notify regulators within required timeframes
- Inform affected users
- Document remediation actions
Delayed reporting increases penalties.
Regulatory Compliance Monitoring
Laws change frequently.
Schedule:
- Annual legal review
- Quarterly compliance checks
- Data processing audits
Compliance Checklist by Region
| Region | Key Regulation | Core Requirement |
|---|---|---|
| EU | GDPR | Consent, breach reporting, data rights |
| USA | CCPA/State Laws | Data access, opt-out rights |
| Canada | PIPEDA | Secure data handling |
| Australia | Privacy Act | Breach reporting, penalty compliance |
| India | DPDP Act | Consent-based processing |
If your white-label EatNow app does not align with these frameworks, expansion becomes legally dangerous.
Compliance is not just paperwork. It is system architecture.
Why Miracuves White-Label EatNow App is Your Safest Choice
Security should never be an afterthought. At Miracuves, it is the foundation.
When you launch a white-label EatNow app with Miracuves, you are not just getting features. You are getting enterprise-grade protection engineered into every layer.
Miracuves Security Advantages
Enterprise-Grade Security Architecture
Miracuves builds platforms using:
- Secure cloud infrastructure
- Network segmentation
- Zero Trust principles
- Hardened backend environments
Security is designed into the system from day one.
Regular Security Audits and Certifications
We follow structured compliance processes aligned with:
- ISO 27001 security frameworks
- SOC 2 best practices
- OWASP Mobile Top 10
- PCI DSS payment security
Independent audits help maintain high security standards.
GDPR / CCPA Compliant by Default
Your white-label EatNow app includes:
- Built-in consent management
- Data access and deletion features
- Secure data processing agreements
- Regional compliance adaptability
This reduces your legal exposure immediately.
24/7 Security Monitoring
Miracuves implements:
- Real-time activity monitoring
- Suspicious login detection
- API traffic analysis
- Automated threat alerts
Continuous monitoring reduces breach response time significantly.
Encrypted Data Transmission
All sensitive information is protected with:
- TLS 1.3 encryption
- AES-256 data encryption at rest
- Secure key management systems
Your customer data stays protected.
Secure Payment Processing
Payment systems are built with:
- PCI DSS-aligned architecture
- Tokenization mechanisms
- Secure gateway integrations
Cardholder data is never exposed unnecessarily.
Regular Security Updates
We provide:
- Scheduled security patches
- Dependency updates
- Vulnerability remediation
- Infrastructure upgrades
Security evolves with new threats.
Insurance Coverage Included
Miracuves-backed projects operate with structured risk management policies.
This adds another layer of business protection.
Why Businesses Trust Miracuves
- 600+ successful projects delivered
- Zero major security breaches reported
- Structured DevSecOps workflow
- Dedicated security response support
- Transparent compliance documentation
In 2026, security is a competitive advantage. Choosing the wrong provider can cost millions. Choosing the right one builds long-term trust.
Final Thought
Our 9k+ successful projects have maintained zero major security breaches. Get a free security assessment and see why businesses trust Miracuves for safe, compliant platforms.
Food delivery platforms handle payments, personal data, and real-time locations. That makes them high-value targets for cybercriminals. A single vulnerability can damage customer trust, trigger legal penalties, and cause financial loss.
FAQs
1. How secure is white-label vs custom development?
Security depends on implementation, not the model. A properly built white-label EatNow app with enterprise controls can be as secure as custom development.
2. What happens if there’s a security breach?
You must activate your incident response plan, notify regulators (within legal timelines), inform users, and fix vulnerabilities immediately.
3. Who is responsible for security updates?
Typically, the development provider manages core updates. Business owners must ensure hosting, access control, and compliance monitoring remain active.
4. How is user data protected in white-label apps?
Through TLS 1.3 encryption, AES-256 storage encryption, secure APIs, tokenized payments, and strict access control.
5. What compliance certifications should I look for?
ISO 27001 alignment, SOC 2 Type II practices, PCI DSS for payments, and GDPR/CCPA compliance.
6. Can white-label apps meet enterprise security standards?
Yes, if built with secure architecture, regular audits, penetration testing, and continuous monitoring.
7. How often should security audits be conducted?
Quarterly vulnerability scans and annual third-party penetration testing are recommended in 2026.
8. What’s included in Miracuves security package?
Enterprise-grade architecture, encrypted infrastructure, compliance-ready framework, monitoring, regular patches, and security documentation support.
9. How to handle security in different countries?
Implement region-specific compliance modules, localized consent management, and data residency controls.
10. What insurance is needed for app security?
Cyber liability insurance, data breach coverage, and professional indemnity insurance are strongly recommended.
Related Articles