You’ve heard the horror stories about data breaches, payment leaks, and fake eCommerce apps stealing user data. And if you’re planning to launch a white-label Temu app, that concern is valid.
In 2026, eCommerce apps handle massive volumes of personal and financial data. One small vulnerability can lead to serious financial loss and trust damage.
The truth is, a white-label Temu app can be either highly secure or dangerously exposed. It all depends on how it’s built, maintained, and audited—and choosing a trusted provider like Miracuves ensures security is handled with enterprise-grade standards from day one.
In this guide, you’ll get an honest breakdown of security risks, real-world standards, and practical ways to ensure your app is safe and compliant.
Understanding White-Label Temu App Security Landscape
What “White-Label Security” Actually Means
White-label security refers to how the underlying app is built, protected, and maintained before you brand it as your own.
You are not starting from scratch. You are relying on a pre-built architecture. That means the security quality depends heavily on the provider.
A secure white-label Temu app includes:
- Pre-tested codebase
- Built-in compliance frameworks
- Secure hosting infrastructure
- Regular updates and patching
If these are missing, risks increase significantly.
Common Security Myths vs Reality
Many businesses assume white-label apps are either completely safe or completely risky. The reality sits in between.
- Myth: White-label apps are less secure than custom apps
Reality: A well-built white-label app can be more secure due to standardized testing - Myth: Security is handled entirely by the provider
Reality: Security is shared between provider and business owner - Myth: Cheap solutions offer the same protection
Reality: Low-cost providers often cut corners on security layers
Why People Worry About White-Label Apps
There are valid reasons behind the concern.
- Lack of transparency in code
- Unclear compliance certifications
- Dependency on third-party infrastructure
- Fear of shared vulnerabilities across multiple apps
These concerns grow stronger in marketplaces like Temu-style apps where multiple vendors and users interact.
Current Threat Landscape for Temu-Type Platforms
Temu-style apps are high-value targets because they handle payments, user data, and logistics.
Common threats include:
- Payment fraud and card data theft
- Fake seller accounts and scams
- API attacks targeting product listings and transactions
- Data scraping and account takeovers
According to recent industry reports, over 43% of eCommerce apps faced at least one security incident in the past year.
Security Standards in 2026
Security expectations have evolved significantly.
In 2026, a secure white-label Temu app must include:
- Zero Trust Architecture
- AI-based fraud detection
- End-to-end encryption
- Real-time monitoring systems
Regulations are also stricter, especially around user data handling and cross-border transactions.
Real-World Statistics on App Security Incidents
- 60% of small eCommerce apps shut down within 6 months of a major breach
- Payment-related attacks increased by over 30% in the last year
- API vulnerabilities account for nearly 50% of modern app breaches
- GDPR penalties can reach up to €20 million or 4% of global turnover
These numbers show that security is not optional anymore. It is a core business requirement.
Key Security Risks & How to Identify Them
Data Protection & Privacy
User Personal Information
A white-label Temu app collects names, addresses, phone numbers, and browsing behavior. This data is highly sensitive.
If encryption or access control is weak, attackers can easily exploit it.
Key risk indicators:
- No data encryption at rest
- Weak user access permissions
- No audit logs
Payment Data Security
Payment processing is one of the biggest risk areas.
If your app is not PCI DSS compliant, card data can be exposed during transactions.
Watch for:
- Storing card details without tokenization
- No secure payment gateway integration
- Missing fraud detection systems
Location Tracking Concerns
Temu-style apps often track user location for delivery and recommendations.
If not handled properly, this can lead to:
- Unauthorized tracking
- Data leaks of user movement
- Privacy violations
Ensure:
- User consent is clearly taken
- Location data is anonymized where possible
GDPR / CCPA Compliance
Non-compliance can lead to heavy penalties.
Common issues:
- No user consent mechanism
- Lack of data deletion options
- Unclear privacy policies
If your app operates globally, compliance is mandatory.
Technical Vulnerabilities
Code Quality Issues
Poorly written code creates hidden vulnerabilities.
Signs of weak code:
- No code review process
- No secure coding standards
- Frequent crashes or bugs
Server Security Gaps
Backend servers store and process critical data.
Risks include:
- Misconfigured cloud servers
- Open ports and weak firewalls
- No intrusion detection systems
API Vulnerabilities
APIs connect your app to vendors, payments, and logistics.
If APIs are insecure:
- Hackers can manipulate transactions
- Data can be intercepted
- Unauthorized access becomes easy
Third-Party Integrations
White-label apps rely heavily on third-party tools.
Each integration adds risk:
- Payment gateways
- Analytics tools
- Shipping APIs
If any third party is compromised, your app is affected.
Business Risks
Legal Liability
If a breach occurs, you are responsible, not just the provider.
This can lead to:
- Lawsuits
- Regulatory penalties
- Contract disputes
Reputation Damage
Users lose trust quickly after a security incident.
Even a single breach can:
- Reduce user retention
- Impact brand credibility
- Affect long-term growth
Financial Losses
Security incidents directly impact revenue.
Examples:
- Refund fraud
- Chargebacks
- Operational downtime
Regulatory Penalties
Governments are strict in 2026.
Penalties can include:
- Heavy fines
- Business restrictions
- Mandatory audits
Risk Assessment Checklist
Use this checklist before launching your white-label Temu app:
- Is all user data encrypted (in transit and at rest)?
- Is the app PCI DSS compliant for payments?
- Are APIs secured with authentication and rate limiting?
- Is there a regular vulnerability testing process?
- Are third-party services audited for security?
- Is there a clear data privacy and consent mechanism?
- Are backup and recovery systems in place?
- Is there a documented incident response plan?
If you cannot confidently answer these, your app is at risk.
Security Standards Your White-Label Temu App Must Meet
Essential Certifications
ISO 27001 Compliance
This is the global standard for information security management.
It ensures:
- Structured risk management
- Secure data handling processes
- Continuous security improvement
Without ISO 27001, there is no formal proof of security maturity.
SOC 2 Type II
SOC 2 focuses on how user data is stored and protected over time.
It verifies:
- Data security controls
- System availability
- Processing integrity
For eCommerce apps, this is a strong trust signal.
GDPR Compliance
If your app serves users in Europe, GDPR is mandatory.
It requires:
- User consent before data collection
- Right to access and delete data
- Transparent data usage policies
Non-compliance can lead to heavy penalties.
HIPAA (If Applicable)
If your Temu app handles health-related products or data, HIPAA may apply.
It ensures:
- Protection of sensitive health information
- Secure data sharing practices
PCI DSS for Payments
This is critical for any app handling payments.
PCI DSS ensures:
- Secure card transactions
- Encrypted payment processing
- Fraud prevention mechanisms
Without this, payment data is at high risk.
Technical Requirements
End-to-End Encryption
All sensitive data must be encrypted from user device to server.
This prevents:
- Data interception
- Unauthorized access
Secure Authentication (2FA / OAuth)
Basic login is no longer enough in 2026.
You need:
- Two-factor authentication
- Social login via OAuth
- Session management controls
Regular Security Audits
Security is not a one-time task.
Your app must undergo:
- Quarterly audits
- Vulnerability assessments
- Compliance checks
Penetration Testing
Ethical hackers test your app for weaknesses.
This helps identify:
- Hidden vulnerabilities
- Exploitable entry points
SSL Certificates
Every connection must be secured with HTTPS.
Without SSL:
- Data can be intercepted
- Browsers may block your app
Secure API Design
APIs must include:
- Authentication tokens
- Rate limiting
- Input validation
This prevents misuse and attacks.
Security Standards Comparison Table
| Security Standard | Purpose | Mandatory for Temu App | Risk if Missing |
|---|---|---|---|
| ISO 27001 | Information security management | Recommended | Weak security processes |
| SOC 2 Type II | Data protection and monitoring | Recommended | Lack of trust and audits |
| GDPR | Data privacy (EU users) | Mandatory (if EU users) | Heavy fines |
| PCI DSS | Payment security | Mandatory | Payment data breaches |
| HIPAA | Health data protection | Conditional | Legal violations |
These standards are not optional anymore. They define whether your white-label Temu app is trustworthy or vulnerable.
Read more : – Business Model of Temu : Complete Strategy Breakdown 2026
Red Flags: How to Spot Unsafe White-Label Providers
Warning Signs
No Security Documentation
If a provider cannot show clear security policies, it is a major risk.
Look for:
- Security architecture documents
- Compliance reports
- Audit records
No documentation usually means weak or untested security.
Cheap Pricing Without Explanation
Extremely low pricing often means corners are cut.
Common compromises:
- No security audits
- Outdated infrastructure
- Shared insecure environments
Security always comes at a cost. If it feels too cheap, it probably is.
No Compliance Certifications
A serious provider will always have certifications.
Red flag if missing:
- ISO 27001
- SOC 2
- PCI DSS
Without these, there is no proof of secure practices.
Outdated Technology Stack
Old frameworks and libraries are easy targets.
Check for:
- Deprecated technologies
- No version updates
- Lack of modern security practices
Poor Code Quality
Even if you cannot see the full code, signs exist.
Indicators:
- Frequent bugs
- Slow performance
- App crashes
These often point to deeper security issues.
No Security Updates Policy
Security threats evolve daily.
If a provider does not offer:
- Regular patches
- Version updates
- Threat monitoring
Your app becomes vulnerable over time.
Lack of Data Backup Systems
Without backups, data loss becomes permanent.
Ensure:
- Automated backups
- Disaster recovery plans
- Redundant storage
No Insurance Coverage
Professional providers carry cyber insurance.
If not, you may bear full financial loss during a breach.
Evaluation Checklist
Before choosing a white-label Temu app provider, ask these questions:
Questions to Ask Providers

Documents to Request
- Compliance certificates
- Security audit reports
- Penetration testing results
- Data protection policies
Testing Procedures
- Request a demo with security features
- Conduct third-party penetration testing
- Check API security and response behavior
Due Diligence Steps
- Review client case studies
- Check past security incidents
- Verify update and maintenance policies
- Evaluate infrastructure (cloud, servers, backups)
Choosing the wrong provider is the biggest security mistake businesses make. Proper evaluation reduces long-term risks.
Best Practices for Secure White-Label Temu App Implementation
Pre-Launch Security
Security Audit Process
Before launch, your app must go through a full security audit.
This includes:
- Vulnerability scanning
- Code-level security checks
- Infrastructure assessment
It helps identify risks before users do.
Code Review Requirements
Every module should be reviewed by security-focused developers.
Focus on:
- Secure coding standards
- Input validation
- Error handling
Unreviewed code is one of the biggest entry points for attackers.
Infrastructure Hardening
Your hosting environment must be locked down.
Key steps:
- Configure firewalls properly
- Disable unused ports
- Use secure cloud configurations
A strong backend reduces attack surface.
Compliance Verification
Before going live, ensure all compliance requirements are met.
Verify:
- GDPR consent flows
- PCI DSS for payments
- Data storage policies
Skipping this step can lead to legal issues later.
Staff Training Programs
Human error is a major cause of breaches.
Train your team on:
- Phishing awareness
- Secure data handling
- Access control practices
Security is not just technical. It is operational.
Post-Launch Monitoring
Continuous Security Monitoring
Once live, your app needs 24/7 monitoring.
This helps detect:
- Suspicious activity
- Unauthorized access
- System anomalies
Early detection prevents major damage.
Regular Updates and Patches
Outdated systems are easy targets.
Maintain:
- Weekly or monthly updates
- Immediate patching for vulnerabilities
- Dependency updates
Incident Response Planning
You must be prepared for worst-case scenarios.
Your plan should include:
- Breach identification steps
- Containment procedures
- User notification protocols
Speed matters during an incident.
User Data Management
Handle user data responsibly.
Best practices:
- Limit data collection
- Store only what is necessary
- Provide user control over data
Backup and Recovery Systems
Always be ready for data loss.
Ensure:
- Daily automated backups
- Secure offsite storage
- Quick recovery mechanisms
Security Implementation Timeline
| Phase | Timeline | Key Actions |
|---|---|---|
| Planning | Week 1–2 | Security requirements, compliance mapping |
| Development | Week 3–8 | Secure coding, API protection, encryption |
| Pre-Launch | Week 9–10 | Security audit, penetration testing, fixes |
| Launch | Week 11 | Go live with monitoring enabled |
| Post-Launch | Ongoing | Updates, monitoring, audits |
A structured approach ensures your white-label Temu app is secure from day one and stays secure over time.
Legal & Compliance Considerations
Regulatory Requirements
Data Protection Laws by Region
Different regions have strict data protection laws in 2026.
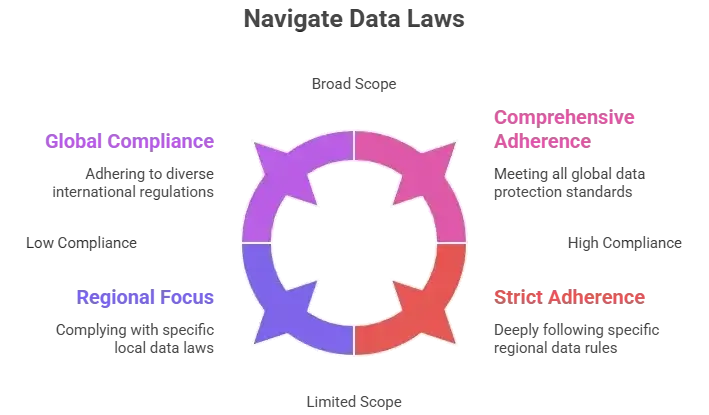
If your app operates globally, you must align with multiple laws.
Industry-Specific Regulations
Depending on your business model, additional rules may apply.
Examples:
- Fintech integrations require financial compliance
- Health-related products may trigger HIPAA
- Cross-border selling involves trade regulations
Ignoring industry rules can lead to operational bans.
User Consent Management
Consent is no longer optional.
Your app must:
- Clearly ask for user permission
- Allow users to withdraw consent
- Track and store consent records
This is a key requirement under most laws.
Privacy Policy Requirements
A proper privacy policy should include:
- What data is collected
- How data is used
- Who data is shared with
- User rights and controls
It must be clear, accessible, and regularly updated.
Terms of Service Essentials
Your terms should define:
- User responsibilities
- Platform limitations
- Dispute handling process
- Seller and buyer rules
This protects your business legally.
Liability Protection
Insurance Requirements
Cyber insurance is becoming essential in 2026.
It covers:
- Data breach costs
- Legal expenses
- Business interruption losses
Without insurance, financial impact can be severe.
Legal Disclaimers
Disclaimers help limit liability.
Include:
- Platform responsibility limits
- Third-party service risks
- User-generated content clauses
User Agreements
Clear agreements reduce disputes.
Ensure:
- Users accept terms before using the app
- Sellers agree to marketplace rules
- Payment policies are transparent
Incident Reporting Protocols
In case of a breach, you must act fast.
Most regulations require:
- Reporting within 24–72 hours
- Informing affected users
- Notifying authorities
Delay can increase penalties.
Regulatory Compliance Monitoring
Compliance is ongoing, not one-time.
You need:
- Regular legal reviews
- Updates based on new laws
- Internal compliance audits
Compliance Checklist by Region
| Region | Key Law | Mandatory Actions |
|---|---|---|
| Europe | GDPR | Consent, data access, right to deletion |
| USA | CCPA/CPRA | Data transparency, opt-out options |
| India | DPDP Act | Consent management, data protection |
| Global | PCI DSS | Secure payment processing |
Failing compliance does not just risk fines. It can shut down your app completely.
Why Miracuves White-Label Temu App is Your Safest Choice
Miracuves Security Advantages
Miracuves builds security into the core, not as an add-on.
- Enterprise-grade security architecture
- Regular security audits and certifications
- GDPR and CCPA compliant by default
- 24/7 security monitoring
- Encrypted data transmission
- Secure payment processing (PCI DSS ready)
- Regular security updates and patches
- Cyber insurance coverage included
Every layer is designed to reduce risk and ensure compliance in 2026.
Why Businesses Trust Miracuves
- 9k+ successful projects delivered
- Zero major security breaches reported
- Proven expertise in eCommerce and marketplace apps
- Dedicated security-first development approach
Final Thought
Don’t compromise on security. A white-label Temu app can be safe, but only if security is treated as a priority from day one.
In 2026, users expect trust, compliance, and data protection by default. Any gap can cost you users, revenue, and reputation. Talk to our team and see why businesses trust Miracuves for safe, compliant platforms.
Choose the right provider, follow security best practices, and stay compliant. That’s how you build a secure and scalable eCommerce platform.
FAQs
1. How secure is white-label vs custom development?
A well-built white-label app can be as secure as custom apps. In many cases, it is more secure due to pre-tested frameworks and regular updates.
2. What happens if there’s a security breach?
You must follow an incident response plan. This includes fixing the issue, notifying users, and reporting to authorities within required timelines.
3. Who is responsible for security updates?
Responsibility is shared. The provider handles core updates, while you must manage configurations, policies, and usage.
4. How is user data protected in white-label apps?
Through encryption, secure servers, access controls, and compliance frameworks like GDPR and PCI DSS.
5. What compliance certifications should I look for?
Look for ISO 27001, SOC 2 Type II, GDPR compliance, and PCI DSS for payment security.
6. Can white-label apps meet enterprise security standards?
Yes, if built by a reliable provider with proper certifications, audits, and infrastructure.
7. How often should security audits be conducted?
It includes encryption, compliance readiness, 24/7 monitoring, regular updates, and secure payment integration.
8. What’s included in Miracuves security package?
At least quarterly, with continuous monitoring and annual penetration testing.
9. How to handle security in different countries?
Follow regional laws like GDPR (EU), CCPA (USA), and DPDP (India). Implement flexible compliance systems.
10. What insurance is needed for app security?
Cyber liability insurance is recommended. It covers breach costs, legal fees, and operational losses.
Related Articles