You’ve heard the horror stories about data breaches, stolen customer data, and hacked eCommerce platforms. And if you’re planning to launch a white-label Shopify app, one question keeps coming up — is it actually safe?
In 2026, eCommerce security is no longer optional. With rising cyberattacks targeting online stores, even a small vulnerability can lead to massive financial and reputational damage. That’s why businesses are increasingly choosing security-first partners like Miracuves, who build white-label Shopify apps with enterprise-grade protection from day one.
This guide gives you an honest, no-fluff breakdown of white-label Shopify app security. You’ll understand real risks, what compliance actually means, and how to build a secure platform from day one.
Understanding White-Label Shopify App Security Landscape
What “White-Label Security” Actually Means
White-label security refers to how the underlying app is built, secured, and maintained before you rebrand and launch it. You are not starting from scratch, but you are fully responsible for how securely it operates once deployed.
A secure white-label Shopify app should include pre-built protections like encrypted databases, secure APIs, and compliance-ready architecture. However, not all providers follow the same standards.
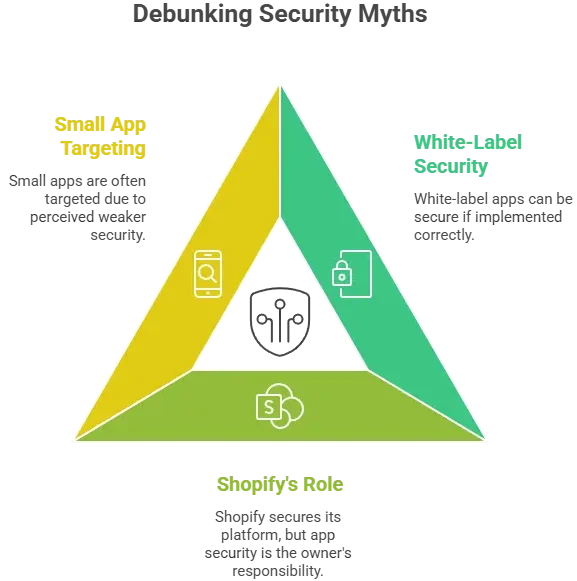
Why People Worry About White-Label Apps
There is a trust gap. Businesses worry about:
- Unknown code quality
- Hidden vulnerabilities
- Lack of transparency from providers
- Shared infrastructure risks
These concerns are valid, especially when dealing with customer data and payments.
Current Threat Landscape for Shopify-Type Platforms
In 2026, eCommerce apps face increasingly sophisticated threats:
- Credential stuffing attacks on user accounts
- Payment fraud and card testing bots
- API exploitation through insecure endpoints
- Malware injections via third-party plugins
Shopify-based ecosystems are attractive targets due to high transaction volumes.
Security Standards in 2026
Modern white-label apps are expected to meet:
- Zero Trust Architecture principles
- End-to-end encryption for sensitive data
- Secure DevOps (DevSecOps) practices
- Continuous vulnerability scanning
Security is now continuous, not a one-time setup.
Real-World Statistics on App Security Incidents
- Over 60% of eCommerce breaches in recent years involved third-party integrations
- Nearly 43% of cyberattacks target small to mid-sized businesses
- API-related attacks have grown by more than 80% in the last two years
- Average cost of a data breach in eCommerce exceeds $4 million globally
These numbers highlight one thing clearly: security gaps in apps are one of the biggest risks in digital commerce today.
Key Security Risks & How to Identify Them
High-Risk Areas You Cannot Ignore
Data Protection & Privacy
User Personal Information
Customer data like names, emails, and addresses are prime targets. If your white-label Shopify app stores this data without encryption or proper access controls, it becomes an easy entry point for attackers.
Payment Data Security
Handling payments means dealing with highly sensitive financial data. Without PCI DSS compliance and tokenization, your app can expose users to fraud and chargebacks.
Location Tracking Concerns
If your app uses geolocation for delivery or analytics, improper storage or sharing of location data can lead to serious privacy violations.
GDPR/CCPA Compliance
Non-compliance can result in heavy penalties. Your app must ensure:
- User consent before data collection
- Right to access and delete data
- Transparent privacy policies
Technical Vulnerabilities
Code Quality Issues
Poorly written or untested code often contains hidden vulnerabilities. These can include:
- SQL injection flaws
- Cross-site scripting (XSS)
- authentication logic
Server Security Gaps
If servers are not properly configured, attackers can exploit:
- Open ports
- Weak firewalls
- Misconfigured cloud storage
API Vulnerabilities
APIs are one of the most attacked components. Risks include:
- Lack of authentication
- Data exposure through endpoints
- Rate limiting failures
Third-Party Integrations
Plugins and external tools can introduce vulnerabilities if not properly vetted. One weak integration can compromise your entire app.
Business Risks
Legal Liability
If user data is compromised, your business is legally accountable. This can lead to lawsuits and compliance investigations.
Reputation Damage
Trust is everything in eCommerce. A single breach can destroy years of brand building.
Financial Losses
Costs include:
- Fraud refunds
- Downtime losses
- Recovery expenses
Regulatory Penalties
Failing compliance standards like GDPR or PCI DSS can result in fines reaching millions.

If you cannot confidently answer “yes” to most of these, your app is exposed to serious risks.
Security Standards Your White-Label Shopify App Must Meet
Essential Certifications
ISO 27001 Compliance
This ensures your app follows internationally recognized information security management practices. It covers risk assessment, data protection, and continuous monitoring.
SOC 2 Type II
SOC 2 Type II verifies how well your systems protect customer data over time. It evaluates security, availability, processing integrity, confidentiality, and privacy.
GDPR Compliance
If you operate in or serve users from Europe, GDPR is mandatory. It focuses on:
- User consent
- Data minimization
- Right to erasure
HIPAA (If Applicable)
If your Shopify app handles healthcare-related products or data, HIPAA compliance becomes necessary to protect sensitive health information.
PCI DSS for Payments
Any app processing payments must follow PCI DSS standards. This includes:
- Secure payment gateways
- Data encryption
- Regular vulnerability scans
Technical Requirements
End-to-End Encryption
All sensitive data must be encrypted both in transit and at rest. This prevents interception and unauthorized access.
Secure Authentication (2FA/OAuth)
Strong authentication mechanisms reduce the risk of unauthorized access. Multi-factor authentication is now a standard expectation.
Regular Security Audits
Security audits help identify vulnerabilities before attackers do. These should be conducted periodically, not just once.
Penetration Testing
Ethical hackers simulate real attacks to find weaknesses in your system. This is critical for proactive security.
SSL Certificates
SSL ensures secure communication between users and your app. Without it, data can be intercepted easily.
Secure API Design
APIs must include:
- Authentication tokens
- Rate limiting
- Input validation
Security Standards Comparison Table
| Security Standard | Purpose | Required For | Risk if Ignored |
|---|---|---|---|
| ISO 27001 | Information security management | All serious businesses | Poor risk control |
| SOC 2 Type II | Data protection over time | SaaS & eCommerce apps | Loss of trust |
| GDPR | User data privacy | EU users | Heavy fines |
| PCI DSS | Payment security | Payment processing apps | Fraud & penalties |
| HIPAA | Health data protection | Healthcare-related apps | Legal consequences |
Meeting these standards is not just about compliance. It is about building trust, preventing breaches, and ensuring long-term business stability.
Red Flags: How to Spot Unsafe White-Label Providers
Warning Signs You Should Never Ignore
No Security Documentation
If a provider cannot clearly explain their security practices, it is a major red flag. Reliable providers always share details about encryption, compliance, and infrastructure.
Cheap Pricing Without Explanation
Unusually low pricing often means compromises in security, infrastructure, or maintenance. Security requires investment, and cutting costs here is risky.
No Compliance Certifications
A provider without ISO, SOC 2, or PCI DSS compliance is likely not following standard security protocols.
Outdated Technology Stack
Old frameworks and unsupported technologies are easier to exploit. Modern security depends on updated systems.
Poor Code Quality
Messy or unstructured code increases the risk of vulnerabilities and makes security audits difficult.
No Security Updates Policy
If there is no clear update or patching process, vulnerabilities will remain open for exploitation.
Lack of Data Backup Systems
Without proper backups, data loss during an attack or failure can be permanent.
No Insurance Coverage
Serious providers often carry cyber insurance. Its absence can indicate lack of maturity in risk management.
Evaluation Checklist
Questions to Ask Providers
- What security certifications do you currently hold?
- How do you handle data encryption and storage?
- Do you conduct regular penetration testing?
- What is your incident response process?
- How frequently do you release security updates?
Documents to Request
- Security compliance certificates
- Audit reports
- Data protection policies
- Incident response plans
- Architecture and infrastructure overview
Testing Procedures
Before finalizing, you should:
- Request a demo with security walkthrough
- Perform basic vulnerability testing
- Check API security using tools like Postman or scanners
- Review authentication and access controls
Due Diligence Steps
- Verify third-party integrations used in the app
- Check client reviews focused on security
- Evaluate uptime and incident history
- Ensure legal agreements include security clauses
Choosing the wrong provider is one of the biggest risks in launching a white-label Shopify app. A careful evaluation process can prevent costly mistakes later.
Best Practices for Secure White-Label Shopify App Implementation
Pre-Launch Security
Security Audit Process
Before launch, conduct a full security audit of the app. This should include:
- Code-level vulnerability scanning
- Infrastructure security checks
- API endpoint validation
A third-party audit is always more reliable than internal reviews.
Code Review Requirements
Every module should go through strict code review. Focus on:
- Secure coding standards
- Input validation
- Error handling
Clean and well-reviewed code reduces long-term risk.
Infrastructure Hardening
Your hosting environment must be secured by:
- Configuring firewalls
- Disabling unused ports
- Using secure cloud configurations
Cloud misconfigurations are one of the most common breach causes.
Compliance Verification
Ensure all required regulations are met before launch:
- GDPR for user data
- PCI DSS for payments
- Regional data laws
Skipping this step can lead to immediate legal issues.
Staff Training Programs
Your internal team should understand:
- Basic cybersecurity practices
- Phishing awareness
- Data handling policies
Human error is still one of the biggest security risks.
Post-Launch Monitoring
Continuous Security Monitoring
Security is not a one-time task. Use monitoring tools to:
- Detect unusual activity
- Track login attempts
- Identify potential breaches early
Regular Updates and Patches
Outdated systems are easy targets. Ensure:
- Frequent security patches
- Framework updates
- Dependency management
Incident Response Planning
Have a clear plan ready for worst-case scenarios:
- Identify the breach source
- Contain the damage
- Notify affected users
- Recover systems quickly
User Data Management
Follow strict policies for:
- Data access control
- Data retention limits
- Secure deletion processes
Backup and Recovery Systems
Maintain regular backups:
- Automated daily backups
- Secure offsite storage
- Quick recovery protocols
Security Implementation Timeline
| Phase | Key Actions | Timeline |
|---|---|---|
| Planning | Security audit, compliance checks | Week 1–2 |
| Development | Code review, secure architecture | Week 3–6 |
| Pre-Launch | Penetration testing, fixes | Week 7–8 |
| Launch | Monitoring setup, backup systems | Week 9 |
| Post-Launch | Continuous updates, audits | Ongoing |
A structured approach ensures your white-label Shopify app is secure from day one and stays protected as it scales.
Legal & Compliance Considerations
Regulatory Requirements
Data Protection Laws by Region
Different regions have strict data laws you must follow:
- Europe (GDPR): Requires explicit user consent, data transparency, and the right to be forgotten
- California (CCPA/CPRA): Users can request access and deletion of their data
- India (DPDP Act 2023 in 2026 context): Focuses on consent-based data processing and user rights
- UK (UK GDPR): Similar to GDPR but with local enforcement
If your Shopify app serves global users, you must comply with multiple regulations simultaneously.
Industry-Specific Regulations
Depending on your business model:
- Fintech integrations require strict financial compliance
- Health-related products may trigger HIPAA requirements
- Cross-border eCommerce must follow international trade and tax laws
User Consent Management
Your app must:
- Clearly ask for user consent before collecting data
- Provide options to opt-out
- Maintain logs of consent records
Privacy Policy Requirements
A strong privacy policy should include:
- What data you collect
- Why you collect it
- How it is stored and protected
- Third-party sharing details
Transparency builds trust and reduces legal risk.
Terms of Service Essentials
Your terms must clearly define:
- User responsibilities
- Platform limitations
- Payment and refund policies
- Dispute resolution mechanisms
Liability Protection
Insurance Requirements
Cyber insurance is becoming essential in 2026. It helps cover:
- Data breach costs
- Legal fees
- Compensation claims
Legal Disclaimers
Disclaimers protect your business from misuse of the platform. They should clearly state limitations of liability.
User Agreements
Well-structured agreements ensure users understand:
- Data usage
- Platform rules
- Security responsibilities
Incident Reporting Protocols
You must have a system to:
- Detect breaches quickly
- Report incidents within legal timelines (e.g., 72 hours under GDPR)
- Notify affected users
Regulatory Compliance Monitoring
Laws evolve frequently. You need:
- Regular compliance reviews
- Legal consultations
- Updates to policies and systems
Compliance Checklist by Region
| Region | Key Law | Mandatory Actions | Risk if Ignored |
|---|---|---|---|
| EU | GDPR | Consent, data rights, breach reporting | Heavy fines up to 4% revenue |
| USA (California) | CCPA/CPRA | Data access & deletion rights | Legal penalties |
| India | DPDP Act | Consent-based processing | Regulatory action |
| UK | UK GDPR | Data protection compliance | Financial penalties |
Legal compliance is not just about avoiding fines. It directly impacts user trust, business credibility, and long-term sustainability.
Why Miracuves White-Label Shopify App is Your Safest Choice
Miracuves Security Advantages
Enterprise-Grade Security Architecture
Miracuves builds every white-label Shopify app with a security-first architecture. This means protection is embedded at every layer, from frontend to backend infrastructure.
Regular Security Audits and Certifications
All apps undergo continuous security audits and follow globally recognized standards like ISO 27001 and SOC 2 practices. This ensures your platform stays compliant and updated.
GDPR/CCPA Compliant by Default
Miracuves solutions are designed to meet international data protection laws from day one. You don’t need to worry about building compliance separately.
24/7 Security Monitoring
Real-time monitoring systems track unusual activities, login attempts, and potential threats, helping prevent attacks before they escalate.
Encrypted Data Transmission
All sensitive data is protected using strong encryption protocols both in transit and at rest, ensuring maximum data security.
Secure Payment Processing
Integrated payment systems follow PCI DSS standards, reducing risks of fraud and protecting customer financial data.
Regular Security Updates
Miracuves follows a strict update cycle to patch vulnerabilities, upgrade frameworks, and maintain system integrity.
Insurance Coverage Included
Unlike many providers, Miracuves includes cyber risk coverage, adding an extra layer of financial protection for your business.
Final Thought
Launching a white-label Shopify app in 2026 is a smart move, but only if security is treated as a priority, not an afterthought.
The real risk is not the white-label model itself. It is choosing the wrong provider or ignoring security fundamentals. With the right standards, audits, and partner, a white-label Shopify app can be as secure as any enterprise platform. Talk to our security expert and see why businesses trust Miracuves for safe, compliant platforms.
In the end, security is what builds trust, and trust is what drives long-term success.
FAQs
1. How secure is a white-label Shopify app vs custom development?
A white-label Shopify app can be equally or more secure if built with proper standards, audits, and compliance. Security depends on implementation, not development type.
2. What happens if there’s a security breach?
You must activate your incident response plan, fix vulnerabilities, notify users, and comply with legal reporting timelines like GDPR’s 72-hour rule.
3. Who is responsible for security updates?
Both the provider and the business owner share responsibility. The provider maintains core security, while you manage configurations and updates.
4. How is user data protected in white-label apps?
Through encryption, secure servers, access control, and compliance with laws like GDPR and CCPA.
5. What compliance certifications should I look for?
ISO 27001, SOC 2 Type II, GDPR, and PCI DSS are essential for most eCommerce apps.
6. Can white-label apps meet enterprise security standards?
Yes, if they follow modern security architecture, regular audits, and compliance frameworks.
7. How often should security audits be conducted?
At least once or twice a year, along with continuous monitoring and periodic penetration testing.
8. What’s included in Miracuves security package?
It includes encryption, compliance readiness, secure payment systems, monitoring, updates, and risk protection measures.
9. How to handle security in different countries?
Follow region-specific laws like GDPR, CCPA, and India’s DPDP Act, and ensure your app supports multi-region compliance.
10. What insurance is needed for app security?
Cyber liability insurance is recommended to cover breach costs, legal fees, and financial damages.
Related Articles