You’ve heard the horror stories about data breaches, leaked payment details, and delivery apps exposing customer locations. In 2026, on-demand grocery apps handle massive volumes of personal and financial data, making them prime cyberattack targets.
If you’re planning to launch a white-label Getir app, safety cannot be an afterthought. One breach can destroy customer trust overnight.
In this guide, you’ll get an honest security assessment of white-label Getir app platforms, real risks to watch for, and practical steps to ensure your app meets enterprise-grade protection standards.
Understanding White-Label Getir App Security Landscape
White-label Getir app security refers to the built-in protection measures within a ready-made grocery delivery platform that you rebrand and launch. Security responsibility is shared between the provider (core infrastructure, codebase) and you (operations, compliance, policies).
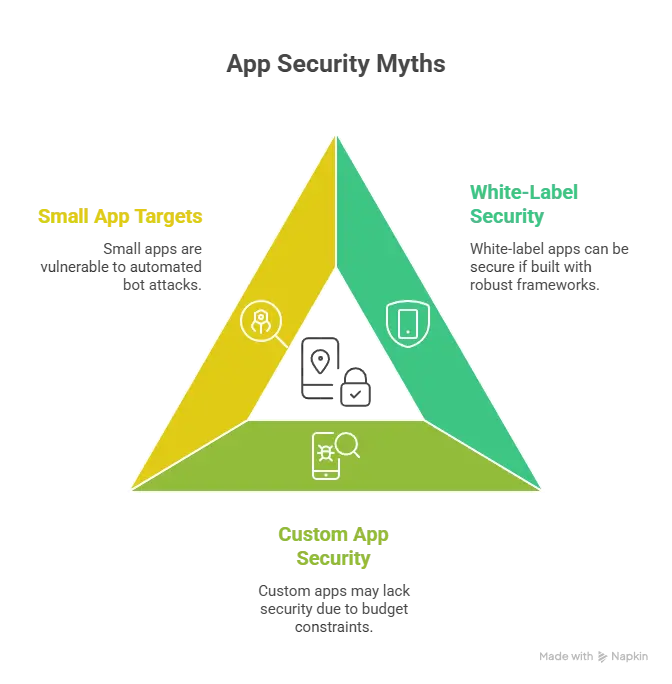
A secure white-label app is not “less secure” by default. The difference lies in how it is developed, maintained, and audited.
Why People Worry About White-Label Apps
- Shared codebase concerns
- Fear of hidden vulnerabilities
- Doubts about compliance certifications
- Lack of transparency from low-cost vendors
These concerns are valid — but avoidable with proper due diligence.
Current Threat Landscape for Grocery Delivery Apps (2026)
On-demand grocery platforms face:
- Payment fraud and card testing attacks
- API exploitation
- Account takeover via weak authentication
- Location data scraping
- Ransomware targeting backend systems
According to recent cybersecurity industry reports, retail and eCommerce apps experienced over 30% growth in credential-stuffing attacks in the past year. Delivery apps are particularly vulnerable due to stored payment methods and saved addresses.
Security Standards in 2026
Modern white-label Getir apps must align with:
- Zero-trust architecture
- Encrypted data in transit and at rest
- Multi-factor authentication
- Secure DevOps (DevSecOps) integration
- Regular third-party penetration testing
Real-World App Security Statistics
- Over 60% of small-to-mid retail apps lack proper API security controls.
- 45% of data breaches in eCommerce involve stolen credentials.
- Payment-related breaches trigger average penalties exceeding $4 million globally.
Security is no longer optional. It is a competitive advantage.
Key Security Risks & How to Identify Them
Launching a white-label Getir app means handling sensitive user data, payment systems, and real-time logistics. Let’s break down the highest-risk areas.
Data Protection & Privacy Risks
User Personal Information
Your app collects names, phone numbers, home addresses, and order history. Weak database encryption or misconfigured servers can expose this data.
Payment Data Security
Saved cards and digital wallets require strict PCI DSS compliance. Insecure tokenization or improper storage creates massive liability.
Location Tracking Concerns
Delivery apps continuously track user and rider locations. If APIs are poorly secured, attackers can scrape real-time coordinates.
GDPR / CCPA Compliance
If your app serves EU or California users, you must provide:
- Data access rights
- Data deletion options
- Explicit user consent
- Transparent privacy policies
Non-compliance can result in heavy fines.
Technical Vulnerabilities
Code Quality Issues
Unoptimized or outdated code increases attack surfaces. Poor input validation can lead to SQL injection or XSS attacks.
Server Security Gaps
Improper cloud configuration is one of the top causes of breaches. Misconfigured AWS or Azure storage buckets remain a common problem.
API Vulnerabilities
Delivery apps rely heavily on APIs for payments, maps, tracking, and notifications. Unsecured APIs allow data leaks and unauthorized access.
Third-Party Integrations
Payment gateways, SMS providers, and analytics tools can introduce vulnerabilities if not vetted properly.
Business Risks
Legal Liability
A breach involving customer addresses or payment data can trigger lawsuits and regulatory action.
Reputation Damage
Customers rarely return after a public security incident.
Financial Losses
Costs include:
- Forensic investigations
- Legal fees
- Regulatory penalties
- Customer compensation
Regulatory Penalties
Data protection authorities are increasing enforcement. Fines can reach 4% of global annual turnover under GDPR.
White-Label Getir App Risk Assessment Checklist
- Is all user data encrypted at rest?
- Is payment processing PCI DSS compliant?
- Are APIs protected with authentication tokens?
- Is 2FA enabled for admin dashboards?
- Are regular penetration tests conducted?
- Is there a documented incident response plan?
- Are backups automated and encrypted?
If you cannot confidently answer yes to these, your white-label Getir app is exposed.
Security Standards Your White-Label Getir App Must Meet
Security is not about promises. It is about certifications, architecture, and proof.
Essential Certifications
ISO 27001 Compliance
Ensures structured information security management systems (ISMS). It proves the provider follows documented risk control processes.
SOC 2 Type II
Validates security, availability, and confidentiality controls over time. Critical for handling customer data in SaaS environments.
GDPR Compliance
Mandatory if serving EU users. Requires lawful data processing, breach notification within 72 hours, and data subject rights management.
HIPAA (If Applicable)
Relevant only if handling health-related grocery or prescription delivery data in certain regions.
PCI DSS for Payments
Required for processing credit and debit cards. Without PCI compliance, your white-label Getir app is legally exposed.
Technical Requirements
End-to-End Encryption
All data must be encrypted:
- In transit (TLS 1.3)
- At rest (AES-256 standard)
Secure Authentication
- Multi-factor authentication (MFA)
- OAuth 2.0 authorization
- Role-based access control (RBAC)
Regular Security Audits
Independent third-party audits at least annually.
Penetration Testing
Quarterly or bi-annual penetration testing to simulate real-world attacks.
SSL Certificates
HTTPS enforced across all user and admin interfaces.
Secure API Design
- Rate limiting
- Token-based access
- API gateway protection
- Input validation
Security Standards Comparison Table
| Security Requirement | Minimum Standard | Enterprise Standard | Mandatory for Grocery Apps |
|---|---|---|---|
| Data Encryption | TLS 1.2 | TLS 1.3 + AES-256 | Yes |
| Payment Security | Basic Gateway | PCI DSS Level 1 | Yes |
| Authentication | Password Only | MFA + OAuth | Yes |
| Compliance | Privacy Policy Only | GDPR + CCPA + SOC 2 | Yes |
| Security Testing | Occasional | Scheduled + Pen Testing | Yes |
If your provider cannot show documentation for these standards, reconsider your decision.
Red Flags: How to Spot Unsafe White-Label Providers
Not all white-label Getir app providers prioritize security. Some focus only on speed and pricing, leaving you exposed.
Warning Signs
No Security Documentation
If a provider cannot share compliance reports, audit summaries, or encryption standards, that is a major risk.
Cheap Pricing Without Explanation
Extremely low pricing often means:
- No security audits
- Shared insecure infrastructure
- Outdated frameworks
No Compliance Certifications
Absence of ISO 27001, SOC 2, or PCI DSS proof indicates weak security governance.
Outdated Technology Stack
Old PHP versions, unsupported libraries, or legacy servers increase vulnerabilities.
Poor Code Quality
No structured architecture, no documentation, and no version control practices are red flags.
No Security Updates Policy
If updates are not scheduled and documented, vulnerabilities remain unpatched.
Lack of Data Backup Systems
Without encrypted automated backups, ransomware can shut down your entire operation.
No Insurance Coverage
Cyber liability insurance shows maturity. Providers without it may not be prepared for incident response.
Evaluation Checklist
Before signing any contract, ask:
Questions to Ask Providers
- Are you PCI DSS compliant?
- Do you conduct regular penetration testing?
- How often are security patches deployed?
- Where is user data hosted?
Documents to Request
- Latest SOC 2 Type II report
- ISO 27001 certificate
- Data Processing Agreement (DPA)
- Penetration testing summary
Testing Procedures
- Request staging access
- Conduct third-party vulnerability scans
- Review API authentication methods
Due Diligence Steps
- Verify certification authenticity
- Review breach history
- Evaluate cloud infrastructure provider
- Confirm incident response timelines
Security transparency separates serious providers from risky ones.
Best Practices for Secure White-Label Getir App Implementation
Security must be planned before launch and maintained after deployment. A white-label Getir app becomes secure through disciplined execution.
Pre-Launch Security
Security Audit Process
Conduct a third-party vulnerability assessment before going live. Identify gaps in encryption, APIs, and server configuration.
Code Review Requirements
Ensure structured code review with secure coding standards (OWASP Top 10 compliance).
Infrastructure Hardening
- Configure firewalls properly
- Disable unused ports
- Implement intrusion detection systems
- Use secure cloud configurations
Compliance Verification
Validate:
- GDPR and CCPA readiness
- PCI DSS payment integration
- Data retention policies
Staff Training Programs
Human error causes many breaches. Train admin staff on:
- Phishing awareness
- Password hygiene
- Access control management
Post-Launch Monitoring
Continuous Security Monitoring
Deploy real-time threat detection and log monitoring systems.
Regular Updates and Patches
Apply framework, plugin, and server updates on a fixed schedule.
Incident Response Planning
Maintain a documented response plan including:
- Breach containment
- Legal notification procedures
- Customer communication strategy
User Data Management
Implement:
- Data minimization
- Automatic deletion policies
- Secure data export systems
Backup and Recovery Systems
- Automated encrypted backups
- Disaster recovery testing
- Offsite backup storage
Security Implementation Timeline
| Phase | Timeline | Key Actions |
|---|---|---|
| Planning | Week 1–2 | Risk assessment, compliance review |
| Pre-Launch | Week 3–6 | Security audit, penetration testing |
| Launch | Week 7 | Final validation, encryption verification |
| Ongoing | Continuous | Monitoring, patching, quarterly testing |
A structured implementation roadmap drastically reduces white-label Getir app security risks.
Read more : – Business Model of Getir : Complete Strategy Breakdown 2025
Legal & Compliance Considerations
Security is incomplete without regulatory compliance. A white-label Getir app must align with regional data protection and commerce laws.
Regulatory Requirements
Data Protection Laws by Region
- EU: GDPR requires lawful processing, breach reporting within 72 hours, and user data rights management.
- USA: CCPA and CPRA mandate transparency and data access rights.
- UK: UK GDPR mirrors EU standards post-Brexit.
- UAE & APAC: Emerging privacy regulations require consent-based data collection.
Industry-Specific Regulations
If your app handles:
- Digital payments → PCI DSS mandatory
- Health-related grocery or prescriptions → HIPAA (US) compliance
User Consent Management
Your app must:
- Capture explicit consent
- Offer opt-out mechanisms
- Log consent records
Privacy Policy Requirements
Must clearly state:
- Data collection types
- Processing purpose
- Third-party sharing
- Data retention duration
Terms of Service Essentials
Include:
- Limitation of liability
- Dispute resolution
- User responsibilities
- Refund and cancellation policies
Liability Protection
Insurance Requirements
Cyber liability insurance should cover:
- Data breach costs
- Legal defense
- Regulatory penalties
- Business interruption
Legal Disclaimers
Transparent disclaimers reduce legal exposure but do not replace compliance.
User Agreements
Properly drafted agreements clarify data usage and reduce disputes.
Incident Reporting Protocols
Define:
- Internal escalation timelines
- Regulatory notification process
- Customer communication guidelines
Regulatory Compliance Monitoring
Compliance is ongoing. Conduct annual reviews to adapt to law changes.
Compliance Checklist by Region
| Region | Key Law | Mandatory Actions |
|---|---|---|
| EU | GDPR | DPO appointment, 72-hour breach reporting |
| USA (California) | CCPA/CPRA | Data access & deletion rights |
| UK | UK GDPR | Data processing agreements |
| Global Payments | PCI DSS | Secure card handling & audits |
Ignoring compliance can cost more than any technical breach.
Read more : – Best Getir Clone Scripts 2025: Launch Your Quick-Commerce App in Days
Why Miracuves White-Label Getir App is Your Safest Choice
Security is not an add-on at Miracuves. It is built into the foundation of every white-label Getir app we deliver.
Miracuves Security Advantages
Enterprise-Grade Security Architecture
Our platforms are designed with zero-trust principles, encrypted databases, and hardened cloud infrastructure.
Regular Security Audits and Certifications
We align with global standards such as ISO 27001, SOC 2 frameworks, GDPR, and PCI DSS compliance requirements.
GDPR / CCPA Compliant by Default
User consent management, data access controls, and deletion workflows are integrated from day one.
24/7 Security Monitoring
Continuous monitoring detects suspicious behavior before it escalates into breaches.
Encrypted Data Transmission
All user, rider, and admin communications are protected with modern TLS encryption.
Secure Payment Processing
PCI-compliant integrations ensure tokenized transactions and safe card handling.
Regular Security Updates
We follow structured patch management cycles to eliminate vulnerabilities proactively.
Insurance Coverage Included
Cyber risk preparedness ensures operational continuity even under unforeseen threats.
Miracuves has delivered 9k+ successful projects with zero major security breaches — because we treat security as business-critical infrastructure, not a feature.
Don’t compromise on security. Miracuves white-label Getir app solutions come with enterprise-grade protection built in. Talk to Our Security Experts Now and launch with confidence.
Final Thought
A white-label Getir app can be extremely safe — but only if security, compliance, and monitoring are treated as non-negotiable priorities.
In 2026, customers trust platforms that protect their data. Choose a provider that proves security with certifications, audits, and transparent processes — not just promises.
FAQs
1. How secure is white-label vs custom development?
A professionally built white-label Getir app can be more secure than custom builds if it follows ISO 27001, SOC 2, and PCI DSS standards with regular audits.
2. What happens if there’s a security breach?
You must activate your incident response plan, contain the breach, notify regulators (within 72 hours under GDPR), and inform affected users.
3. Who is responsible for security updates?
Core infrastructure security is handled by the provider, while operational and policy-level security remains your responsibility.
4. How is user data protected in white-label apps?
Through AES-256 encryption at rest, TLS encryption in transit, secure authentication, and role-based access control.
5. What compliance certifications should I look for?
ISO 27001, SOC 2 Type II, GDPR compliance, and PCI DSS for payment-enabled apps.
6. Can white-label apps meet enterprise security standards?
Yes, if built with zero-trust architecture, secure APIs, and third-party penetration testing.
7. How often should security audits be conducted?
At least annually, with quarterly vulnerability scans and regular penetration testing.
8. What’s included in Miracuves security package?
Enterprise-grade architecture, encrypted infrastructure, compliance-ready framework, regular audits, and ongoing monitoring.
9. How to handle security in different countries?
Implement region-specific compliance modules such as GDPR (EU) and CCPA (California), with localized privacy policies.
10. What insurance is needed for app security?
Cyber liability insurance covering breach costs, legal defense, regulatory fines, and business interruption.
Related Articles